case studies & whitepapers
to help you develop your
cyber security & risk mitigation
strategies.
The Quod Blog
Latest cyber security and risk insights, analysis and thought leadership delivered to your inbox.
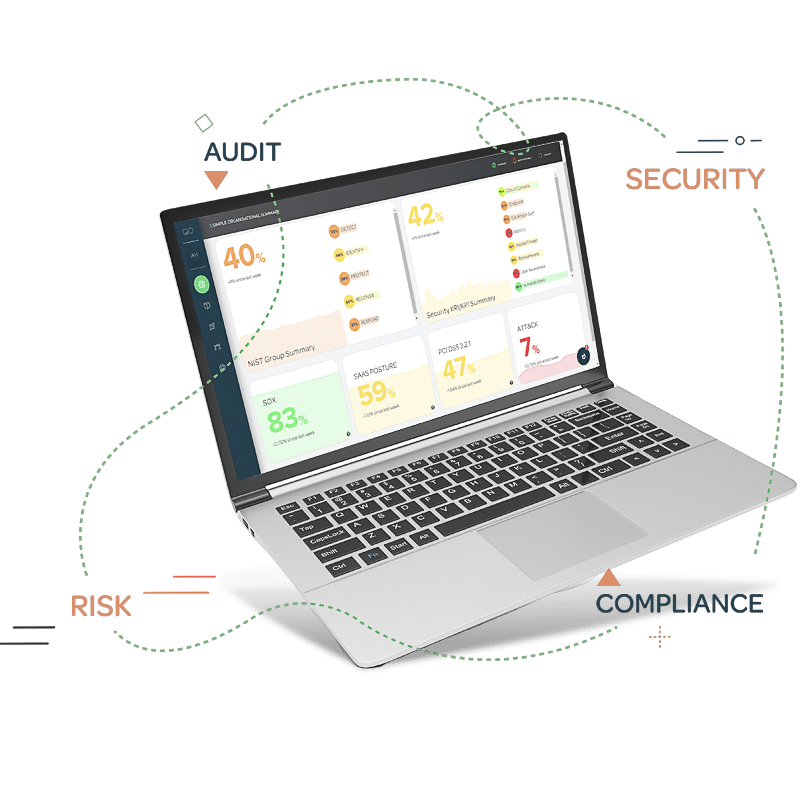
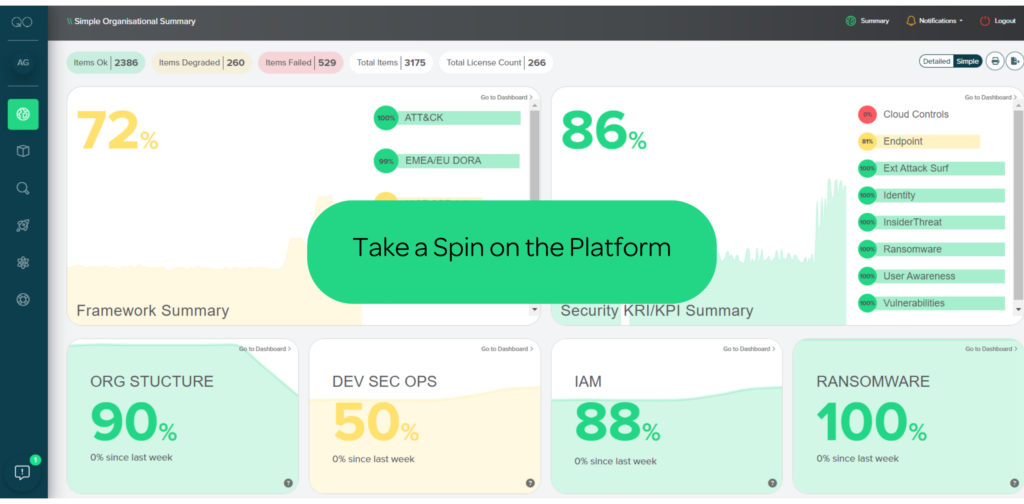
Interactive Demos
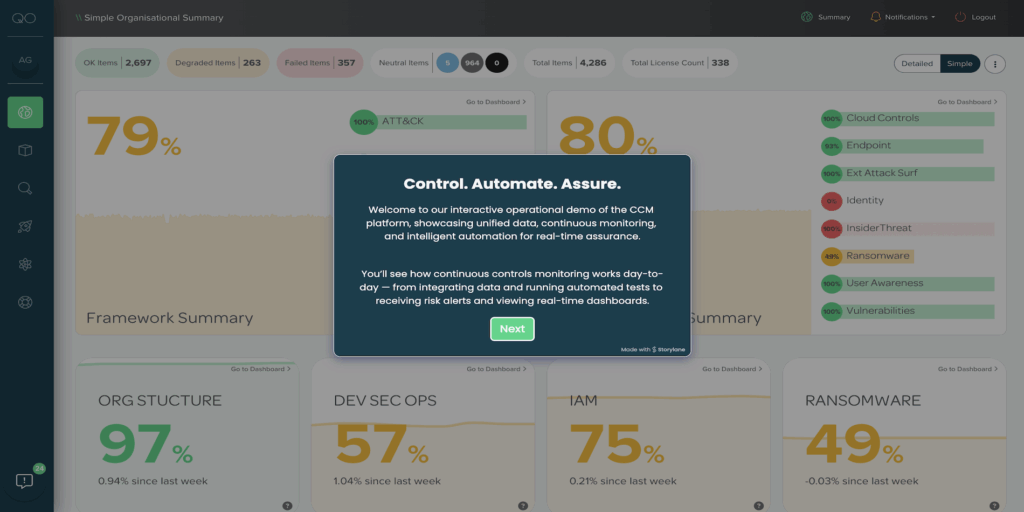
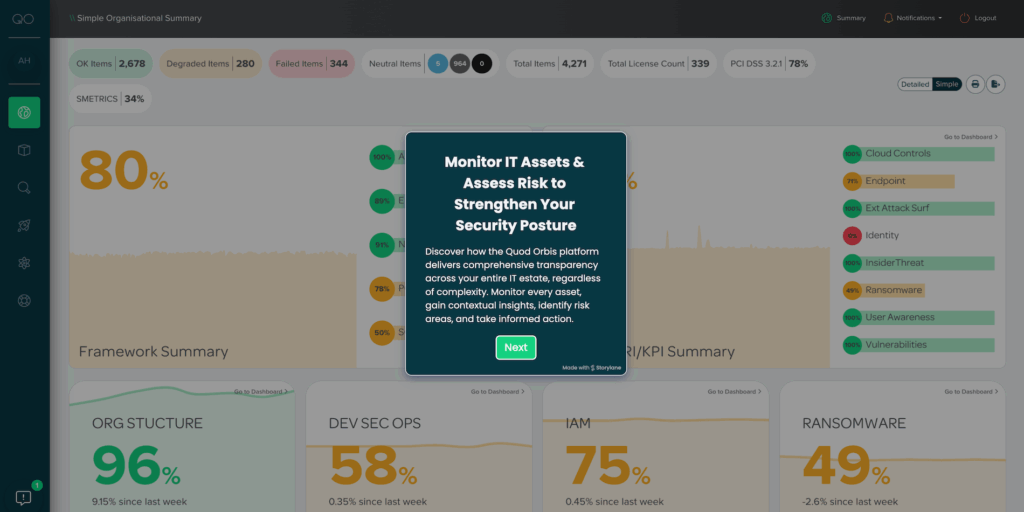
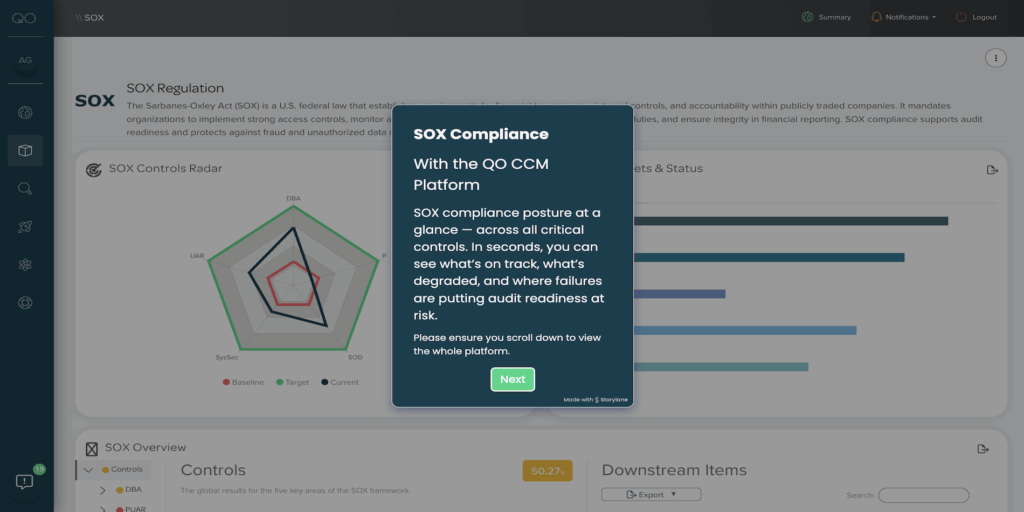
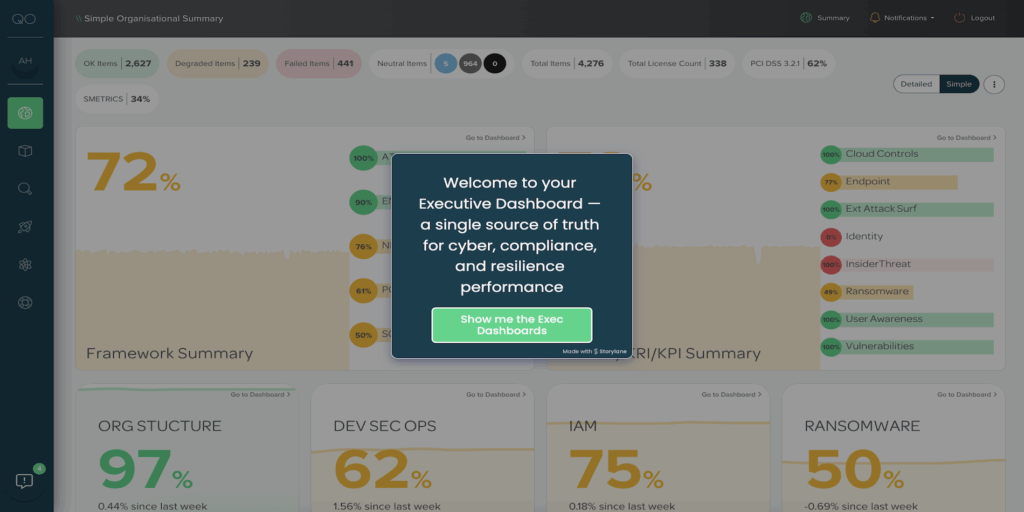
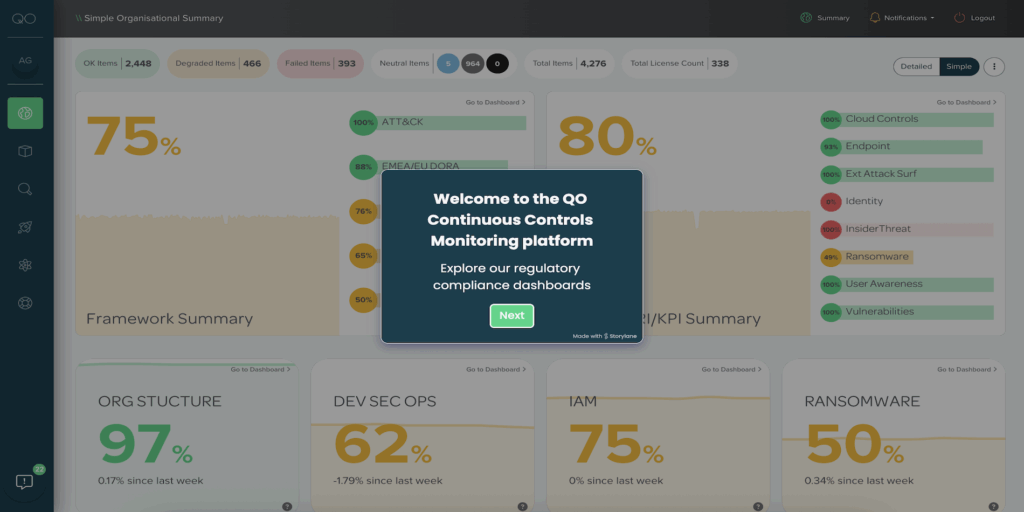
Navigate our guided tour to experience first-hand how our CCM platform provides complete oversight into your cyber security, risk and compliance posture. We can connect to any data, monitor any control and align to any framework.
You can expect to see;
- How to navigate the platform
- Overview of summary & detailed dashboards
- Ransomware & compliance dashboards
- How to drill into the evidence of the reports
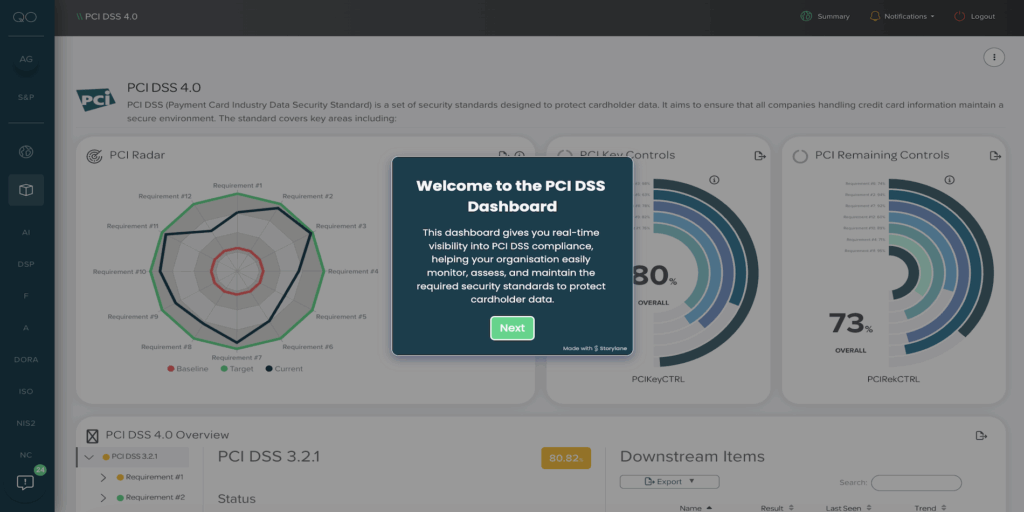
Explore our PCI DSS dashboard in action—take the interactive tour and discover how continuous controls monitoring simplifies compliance and strengthens data security.
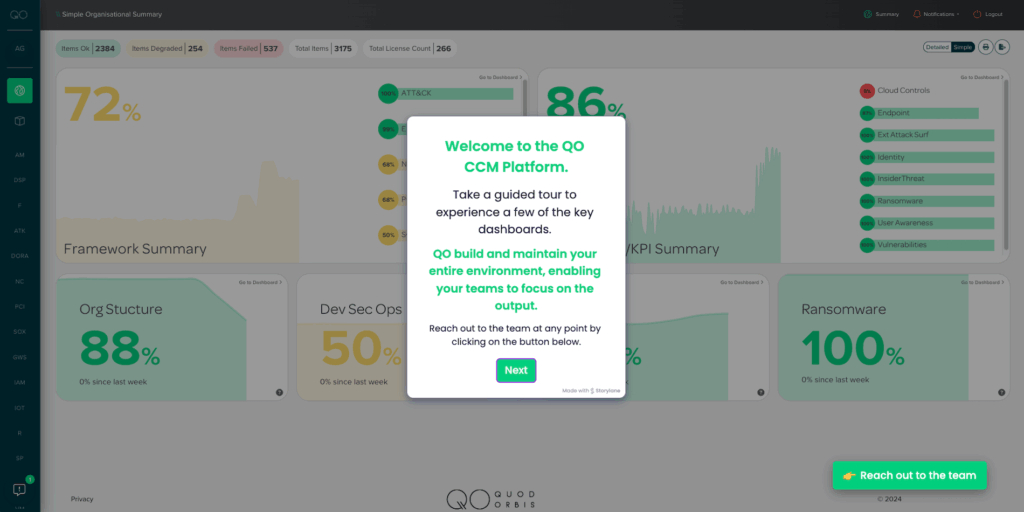
Explore our guided tour to see how our CCM platform delivers full visibility into your cybersecurity, risk, and compliance.
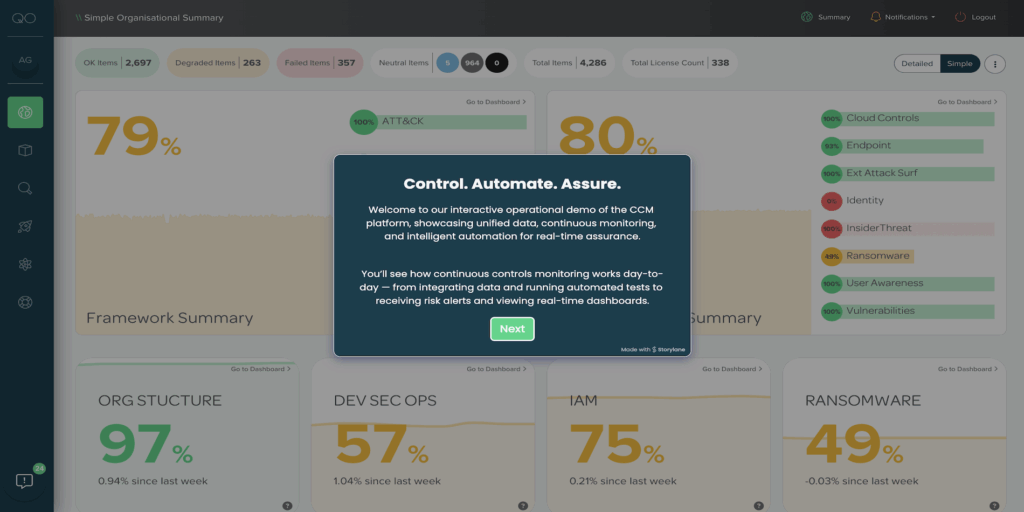
Continuous controls monitoring in action: automated tests, real-time alerts, and unified dashboards for assurance.
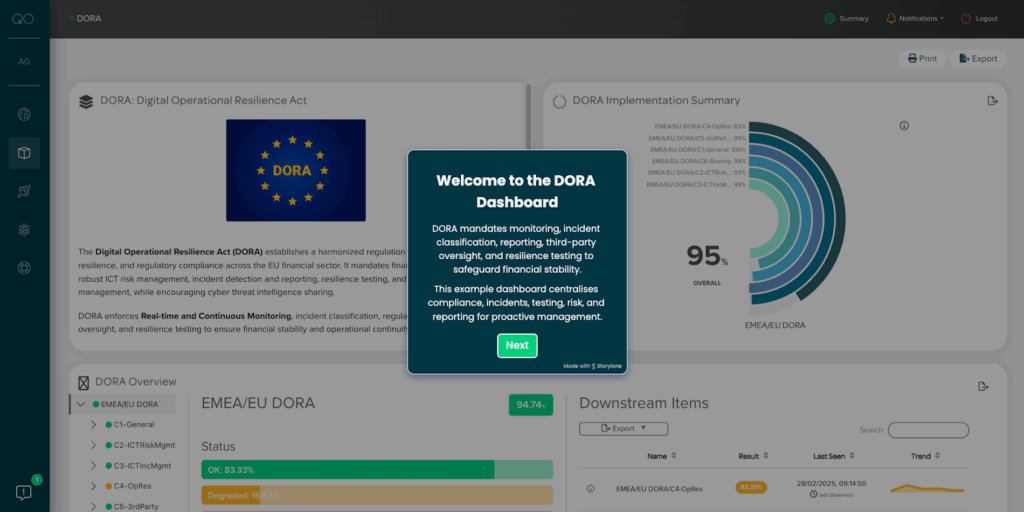
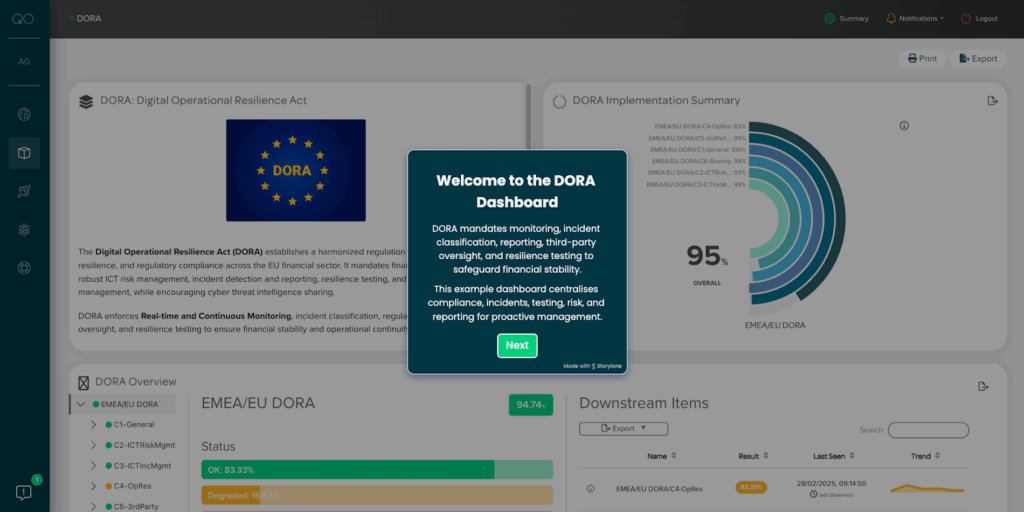
Take our guided tour to discover how our CCM platform seamlessly aligns with DORA requirements and supports your compliance efforts.
Continuous controls monitoring in action: automated tests, real-time alerts, and unified dashboards for assurance.
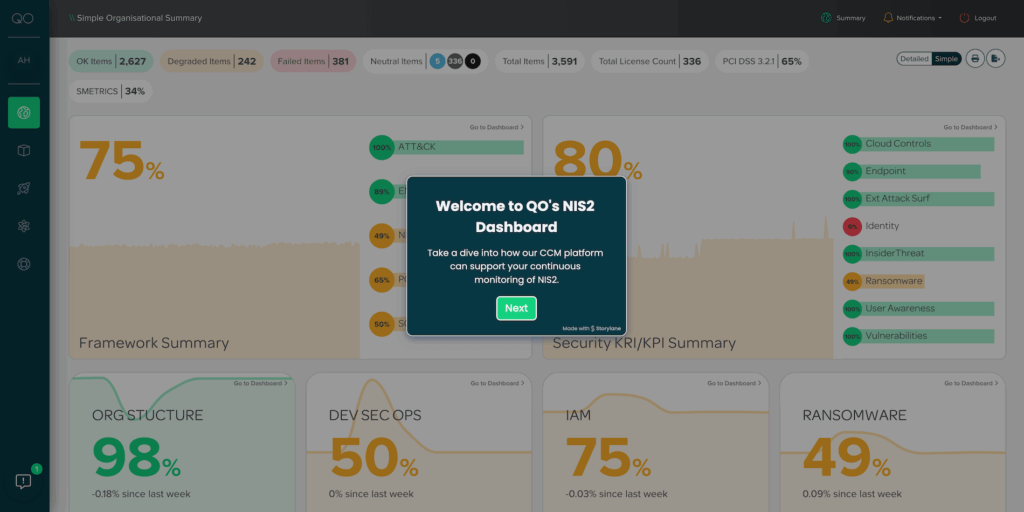
Discover how our CCM platform is built to meet NIS2 requirements—take the tour and see how we simplify your compliance journey.
Take our guided tour to discover how our CCM platform seamlessly aligns with DORA requirements and supports your compliance efforts.
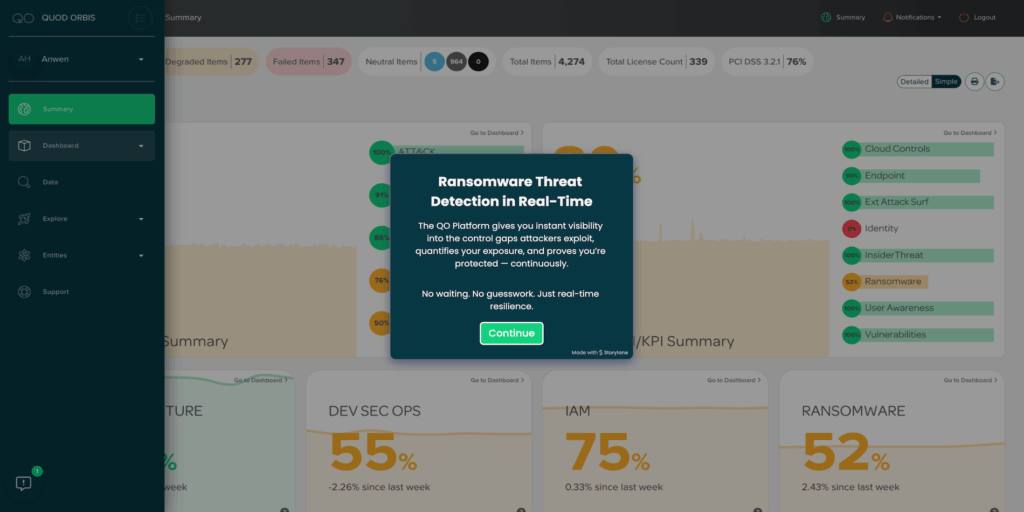
Explore our ransomware demo to catch early warning signs before attacks happen. Clear, data-driven alerts show what needs fixing—fast. See how quick insights help you stay ahead and strengthen your defences.
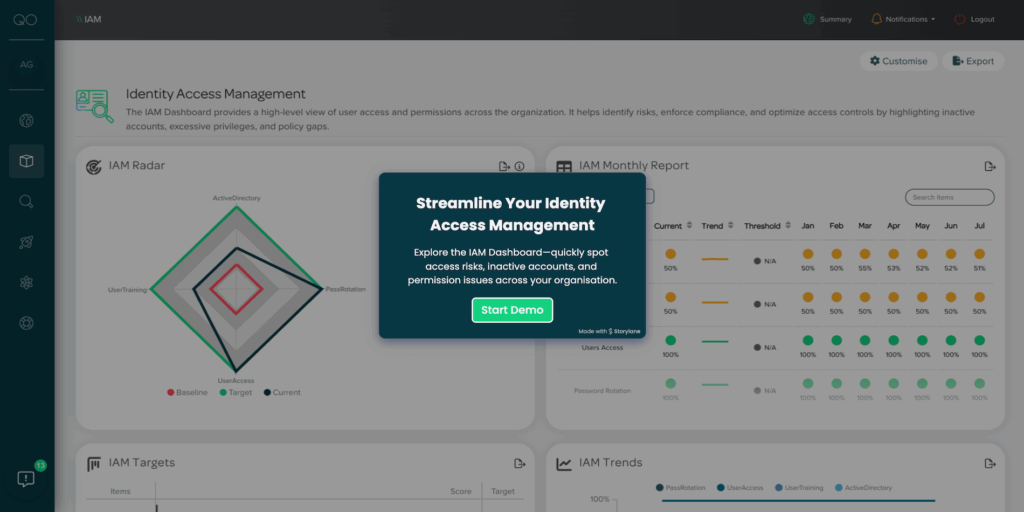
Experience our CCM platform in action—take the interactive tour and see how we simplify identity and access management through continuous controls monitoring.
Explore asset visibility in action. With just a few clicks, see how the platform tracks every asset, highlights risks, and gives you full control. Quick, clear, and interactive—take the tour now.
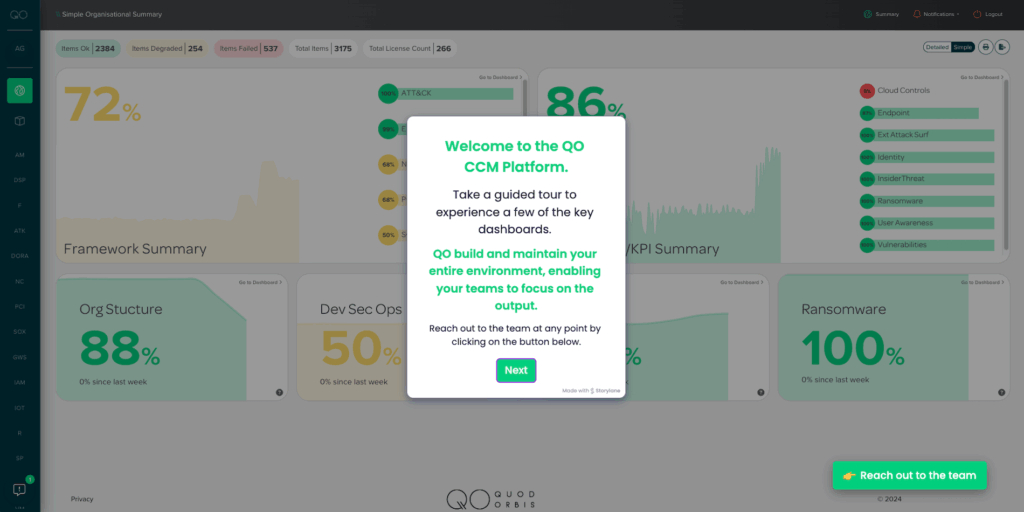
Explore our guided tour to see how our CCM platform delivers full visibility into your cybersecurity, risk, and compliance.
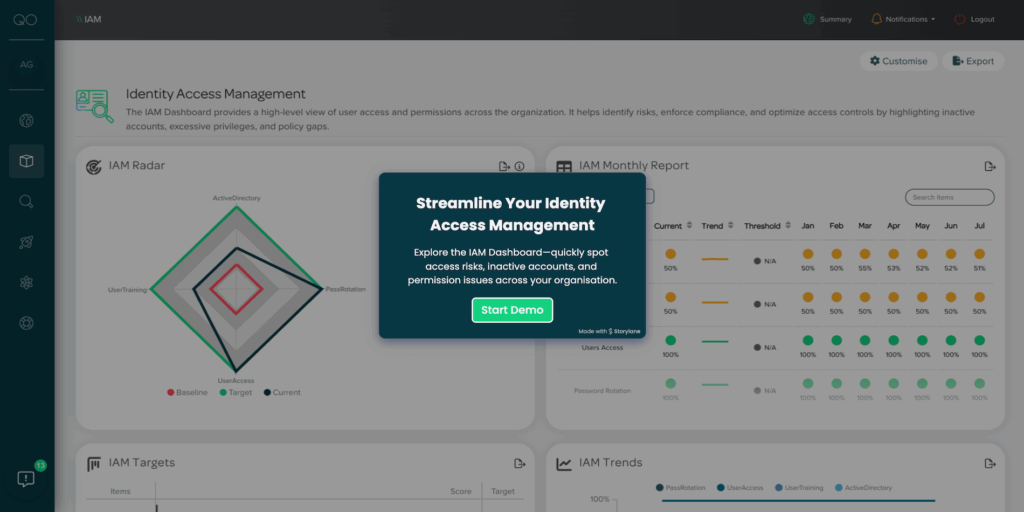
Experience our CCM platform in action—take the interactive tour and see how we simplify identity and access management through continuous controls monitoring.
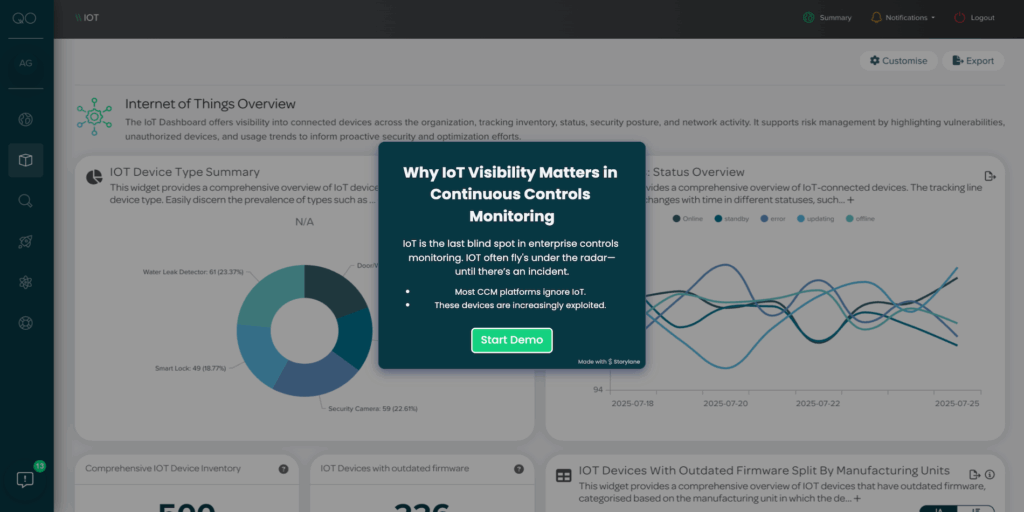
Explore our CCM platform in action—take the interactive tour and see how we simplify continuous controls monitoring for your IoT ecosystem.
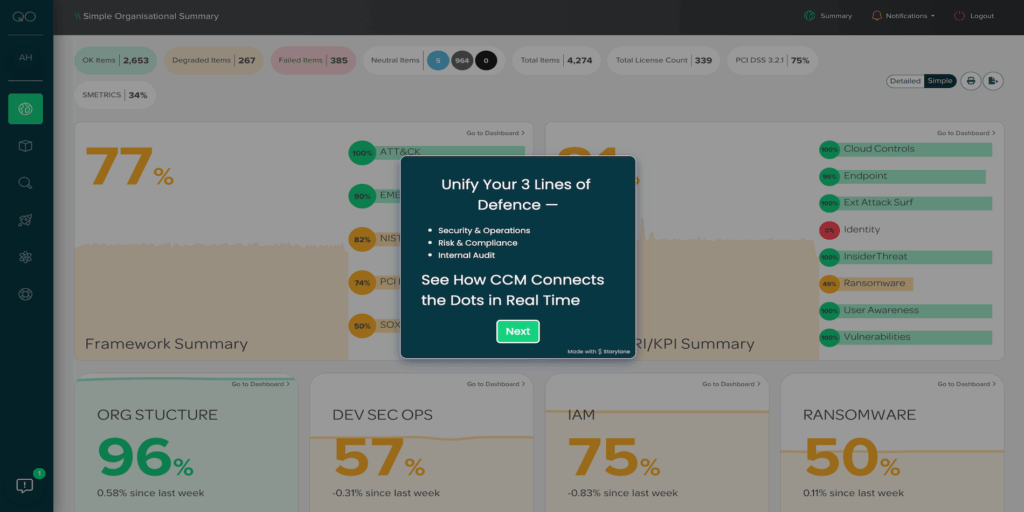
Explore our CCM platform in action—take the interactive demo and see how we strengthen and streamline your Three Lines of Defence framework.
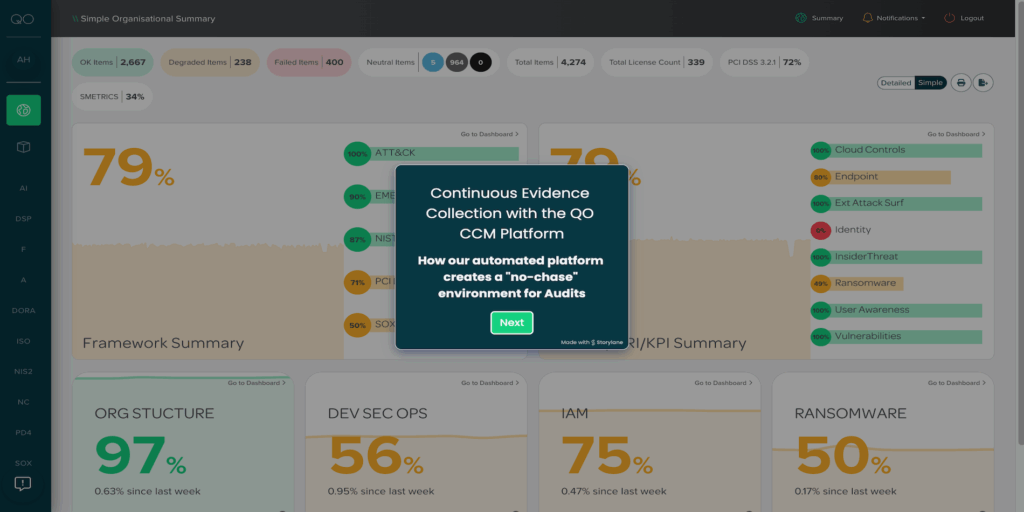
Explore our CCM platform in action—take the interactive tour and see how we streamline automated evidence collection for continuous controls monitoring.
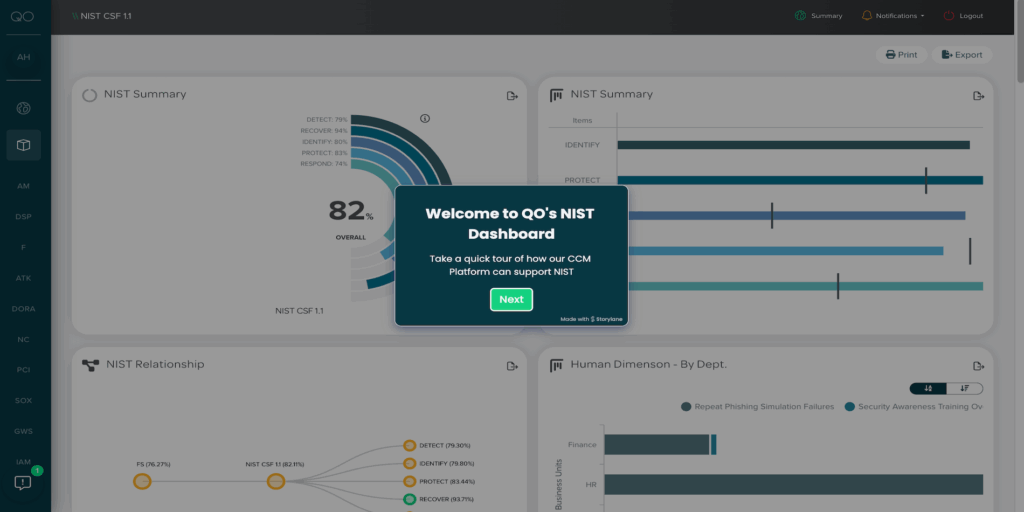
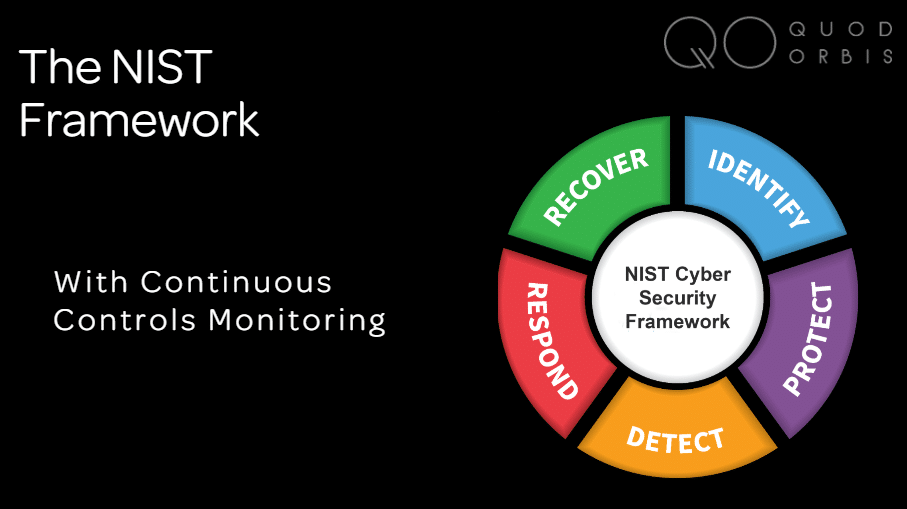
Discover how our CCM platform supports NIST standards—take the interactive demo and see how we simplify your compliance and controls monitoring journey.
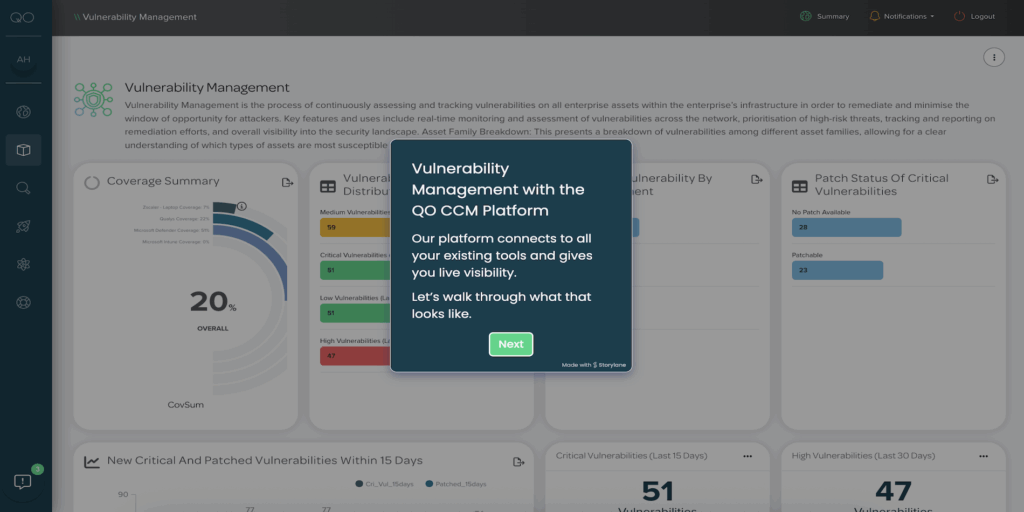
Experience our CCM platform in action—take the interactive demo and see how we simplify and automate vulnerability management across your organisation.
Explore our CCM platform in action—take the interactive demo and see how we strengthen and streamline your Three Lines of Defence framework.
Experience our CCM platform in action—take the interactive tour and see how we simplify identity and access management through continuous controls monitoring.
Take our guided tour to discover how our CCM platform seamlessly aligns with DORA requirements and supports your compliance efforts.
Featured Resources

Continuous Controls Monitoring (CCM) is key to effective risk management, yet misconceptions persist. This article debunks five common myths, clarifying its true benefits.
Our latest research analyses how a lack of visibility jeopardises business continuity, leaving organisations unprotected to risks like downtime, security breaches, and compliance failures.

Our latest whitepaper in partnership with Secon Cyber offers an in-depth exploration of DORA, breaking down its key components, compliance requirements, and the strategic opportunities it presents for your organisation.
Videos & Webinars
Videos
42 Videos






























- All
- Infographics & Ebooks
- Datasheets
- Case Studies
- Research & Whitepapers
Register for updates
Keep up to date with the latest CCM, cyber security and risk news.
Book a demo