Cyber Security Consultancy
Identity & Access Management (IAM)
Secure Access for Users, Systems, and Partners. Protect your organisation with IAM solutions. Manage user access, enforce policies, and reduce insider risk with SSO, MFA, and Privileged Access Management.

Secure Access for People and Systems
Uncontrolled access is one of the biggest cybersecurity risks organisations face today. Mismanaged accounts, third-party users, and privileged access can lead to breaches, data loss, and regulatory non-compliance.
Our Identity & Access Management (IAM) services ensure the right people have the right access at the right time, keeping your systems secure while simplifying operations.
Our IAM Strategy
Our IAM strategy is designed to secure access, reduce risk, and simplify compliance across all users, systems, and third-party connections.
We work with organisations to:

Role & Responsibility Definition
Clearly define user roles and job functions to ensure access follows the principle of least privilege.

Access Policies & Governance
Develop enforceable policies covering password management, session controls, privileged account handling, and approval workflows.

Lifecycle Management
Automate onboarding, role changes, and off boarding to prevent orphaned accounts and reduce insider risk.

Privileged Access Controls
Protect high-risk accounts with just-in-time access, approvals, and activity logging for auditing.

Third-Party & Vendor Access Management
Secure external access while ensuring compliance with your access policies.

Compliance Alignment
Meet GDPR, ISO 27001, NIST, and sector-specific requirements with audit-ready evidence.
Continuous Monitoring & Reporting
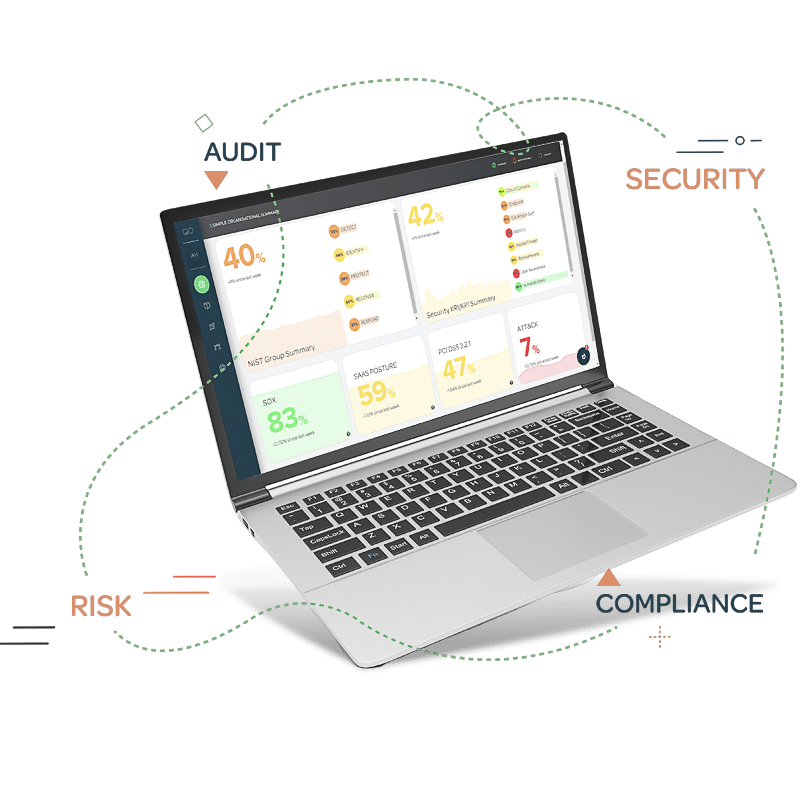
Integrate IAM with tools like CCM to track access anomalies and provide actionable risk insights.
By implementing a strategic IAM framework, your organisation reduces risk, strengthens compliance, and maintains operational efficiency.
Our Implementation
We deploy IAM solutions that balance security, usability, and efficiency:
- Single Sign-On (SSO): Simplify authentication and reduce password fatigue.
- Multi-Factor Authentication (MFA): Add an extra layer of protection against account compromise.
- Privileged Access Management (PAM): Control, monitor, and audit high-risk accounts.
These technologies ensure secure access for employees, contractors, and partners while minimising operational friction.

Business Value Delivered
IAM delivers measurable benefits:
- Reduce insider and third-party access risks.
- Simplify onboarding and offboarding processes.
- Demonstrate compliance with regulatory frameworks.
- Integrate with broader cybersecurity and risk management initiatives, enhancing operational resilience.
What Sets Us Apart
Interlinking IAM with CCM and SOC
IAM works seamlessly with Continuous Controls Monitoring (CCM) and our Security Operations Centre (SOC) to provide full-spectrum security and compliance coverage. IAM ensures proper user access and privileges, while CCM continuously verifies that controls are operating effectively. By feeding IAM and SOC data into CCM dashboards, organisations can detect anomalies, validate controls, and remediate risks faster, achieving proactive security and continuous assurance across IT, cybersecurity, and operational processes.
Secure your users and systems with IAM. Contact Us to implement robust access controls that protect your organisation from internal and external threats.
Explore our CCM platform here.

Get in touch
Contact us today for more information on our cyber and risk consultancy services, or for an initial chat about your needs or concerns.
Alternatively, you can book a meeting directly here.