“Asset visibility” is a recognised core concept in Information Security and there are few factors which are more important today than knowing exactly what you have in your estate. Assets can be anything from physical devices also known as hardware, buildings or other infrastructure and non-tangible resources for example cloud resources, and data. Gaining asset visibility is the cardinal starting point for rolling out any cybersecurity programme assuming of course that the aim is to implement the programme successfully. Of course, I cannot refer to people (once upon a time, but hopefully never again referred to as “wetware” or “meatware”) as assets but it is important that you recognise their contribution and importance in the security of any organisation. Humans are the most essential link in any cybersecurity chain.
- What assets do we have within our estate?
- What of these assets do we need?
- Which of these assets do we own or manage?
- Which of these assets did/do we pay for?
- Which of these assets would we rather not have residing in our estate?
- If we were to rank the assets identified above by order of importance to the organisation, which of them are the most important?
After the answers to these have been obtained following an asset discovery exercise, the following may be the next set of considerations:
- What are the gaps in our controls?
- Which cybersecurity controls will aid our goal of ensuring “beyond-adequate” security for our assets?
- With data being described by some as “the new oil” as a way of highlighting its potential importance, do we as an organisation have the right controls in place to protect the data we own or handle?
- When factors such as industry verticals or attack types faced by our organisation are considered, which of these identified controls are the most important?
- What is the best plan for putting the right controls in place to ensure we secure our assets beyond achieving the static, bare minimum, “repeat-manually-every-six-months-or-every-quarter” exercise of ticking boxes?
- As these controls are being rolled out, how do we measure improvements to our security posture and ongoing cybersecurity strategy? What is the best way to identify existing cybersecurity solutions overlaps, controls overlaps or even persisting, stubborn gaps in our security solutions or controls?
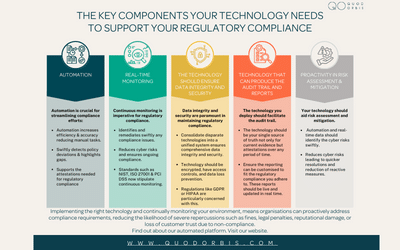
- Do we manage all the above manually? How limiting – or even detrimental – is the manual approach to managing cybersecurity controls? Does it introduce the risk of mistakes and therefore erroneous and potentially costly decisions missed gaps leading to fines for poor security culture resulting in reputational damage, and so on. Is an automated approach preferable, with all the benefits of speed, reduced errors, repeatability, scheduling, measurability and the possibility to make rapid adjustments to a cybersecurity roadmap as required?
With the increasing types and numbers of devices and applications and the volume, variety and velocity of production of new data and recognising the reality of Bring Your Own Device (BYOD) and working from home options being adopted by an increasing number of companies due to the benefits they provide (cheaper or zero office rent costs, lower company bills, potentially more productive employees, etc.) – it is critical that organisations gain real-time, trustworthy visibility into which controls affect the assets that are in use as part of their estate and where the gaps in their security coverage is.
Knowing which controls you have in place or otherwise in real-time helps you plan for the best way to secure your asset estate. Identifying the controls needed to ensure the security of these assets and, unwittingly or otherwise, to support compliance requirements is a smart approach to security today. The alternative is an absence of visibility into some very vital security measurements.
Organisations can choose to capture, measure and review their organisation’s controls using lists and documentation which they create, share and manage manually. Alternatively organisations can offload the task to an automated system that consumes their controls in real-time if they have any controls in place and provides them with actionable insights into the coverage across all their assets, recommendations for the smartest way to improve your cybersecurity posture over a pre-agreed period as well as making recommendations for managing the current risks using mitigation techniques, among other approaches.
The options are quite clear: you can choose to drive to the market, or you can walk there – but you can’t complain if the person who opts to shop online gets there first and gets the best produce. Visibility, Speed and Relevant recommendations.