Continuous Controls
Monitoring
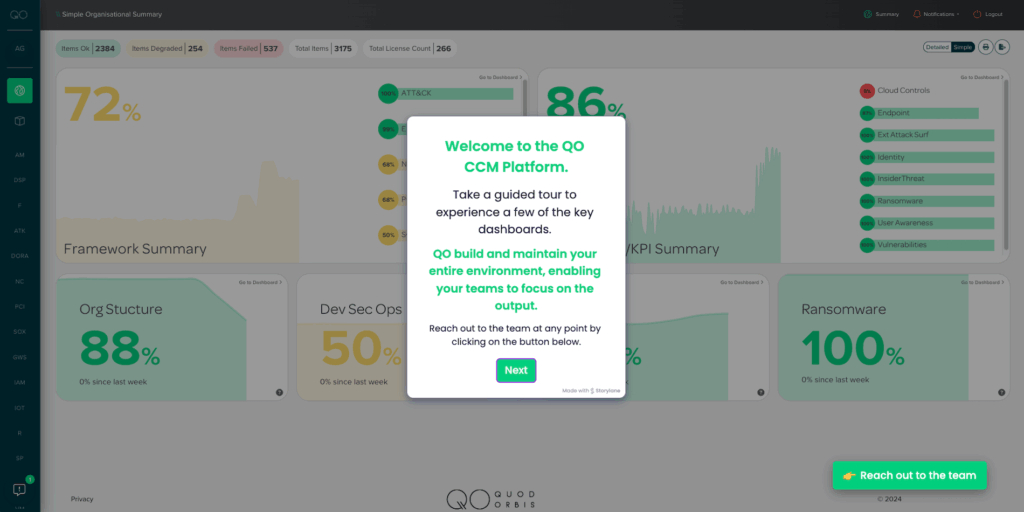
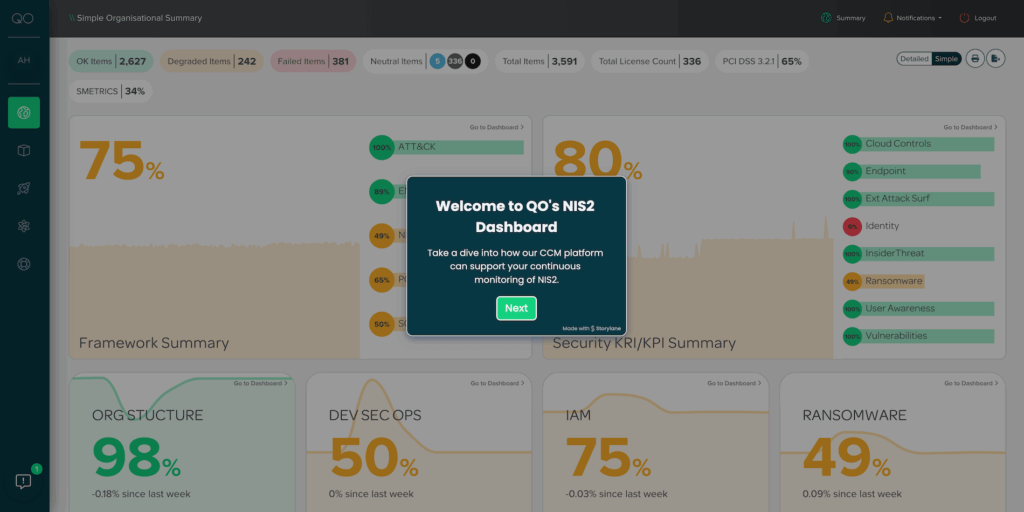
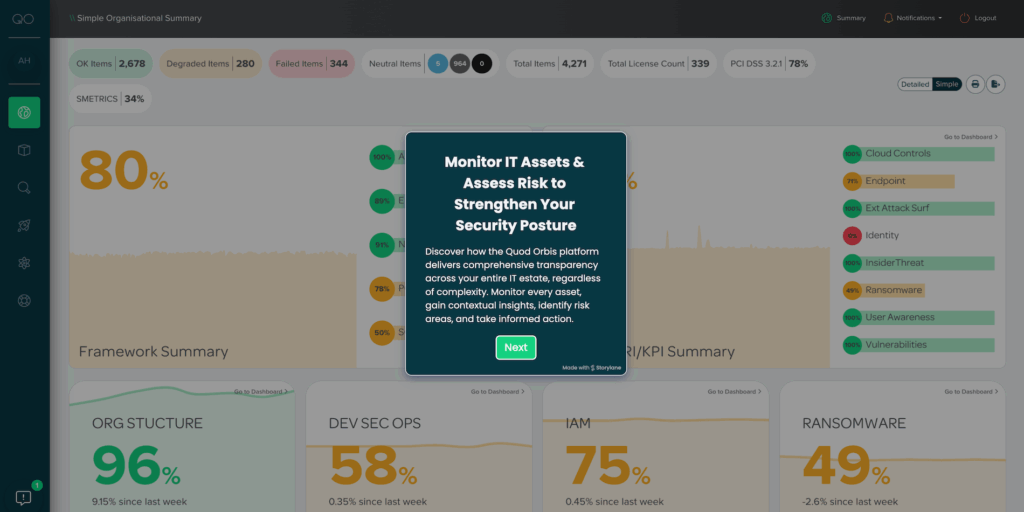
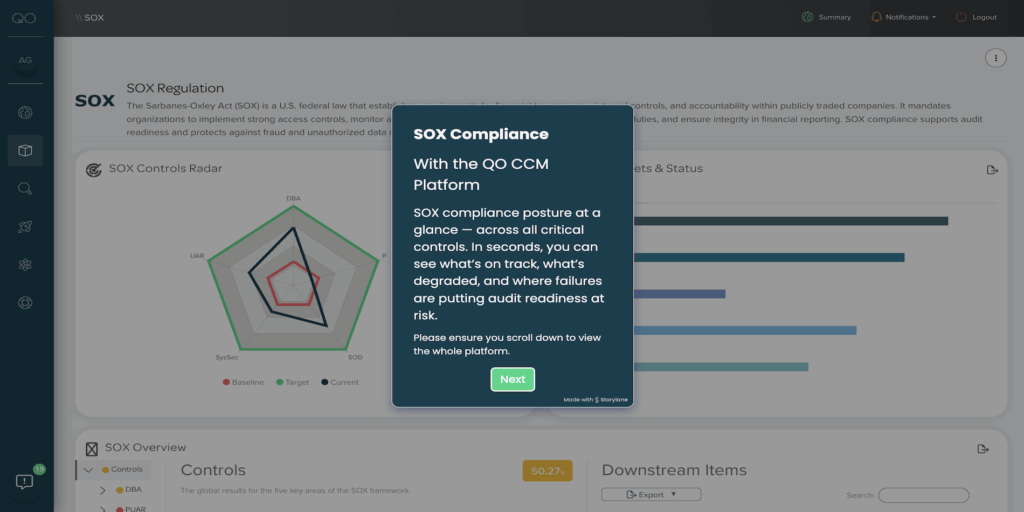
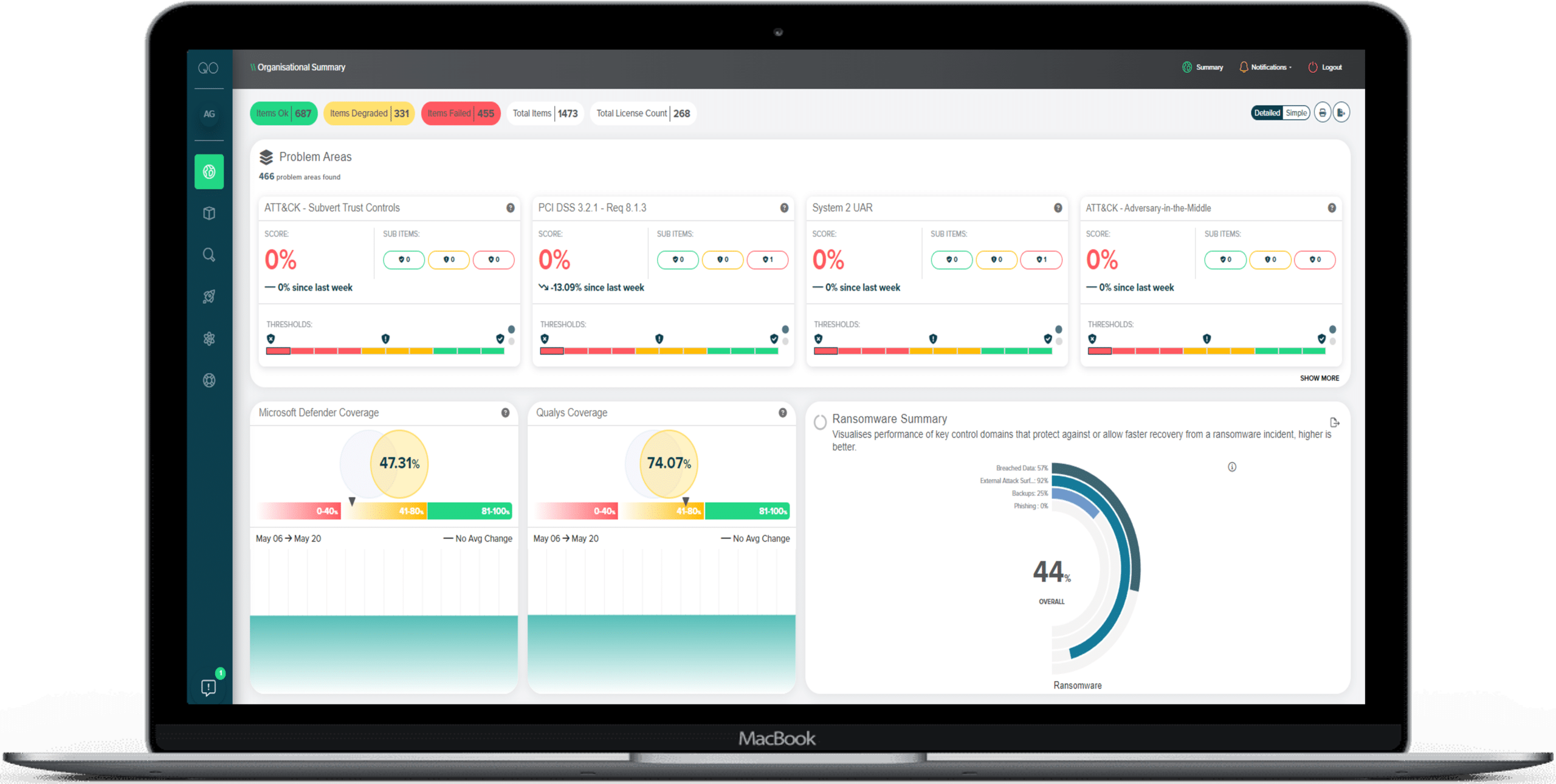
Take a Tour of Our Platform
Any Control,
Any Framework
Intelligence
and business decisions
our CCM platform?
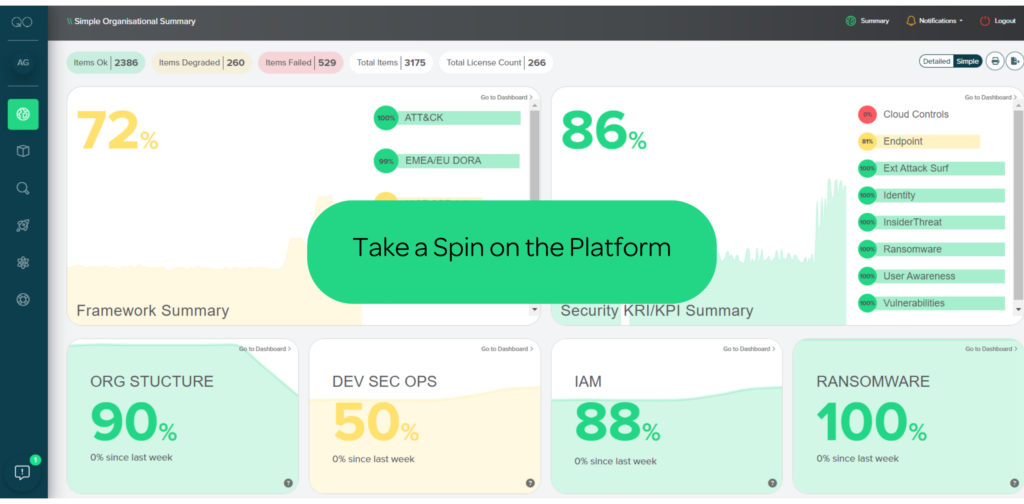
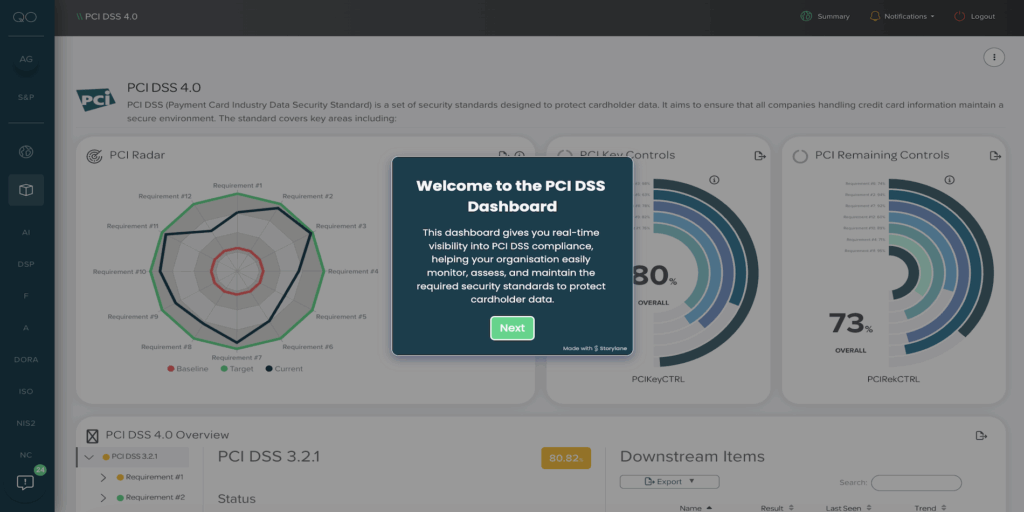
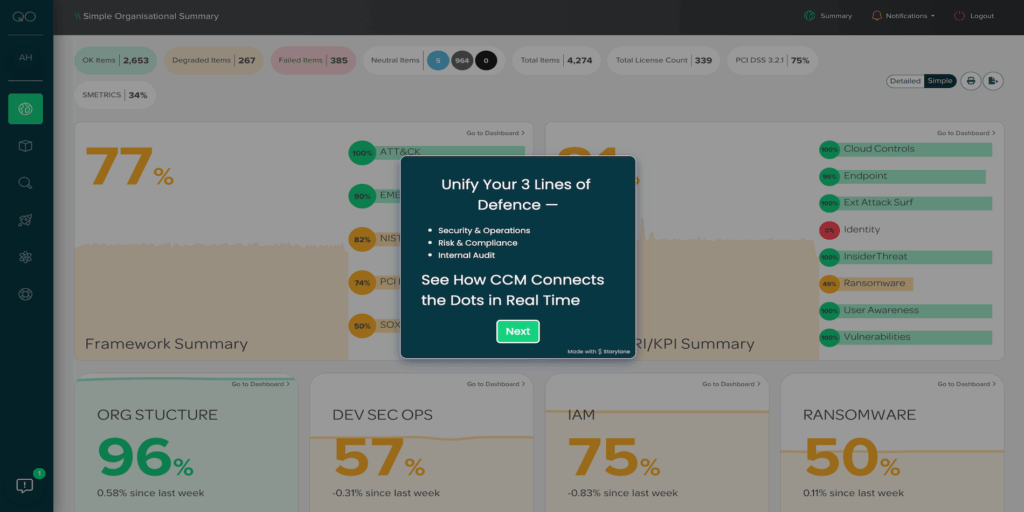
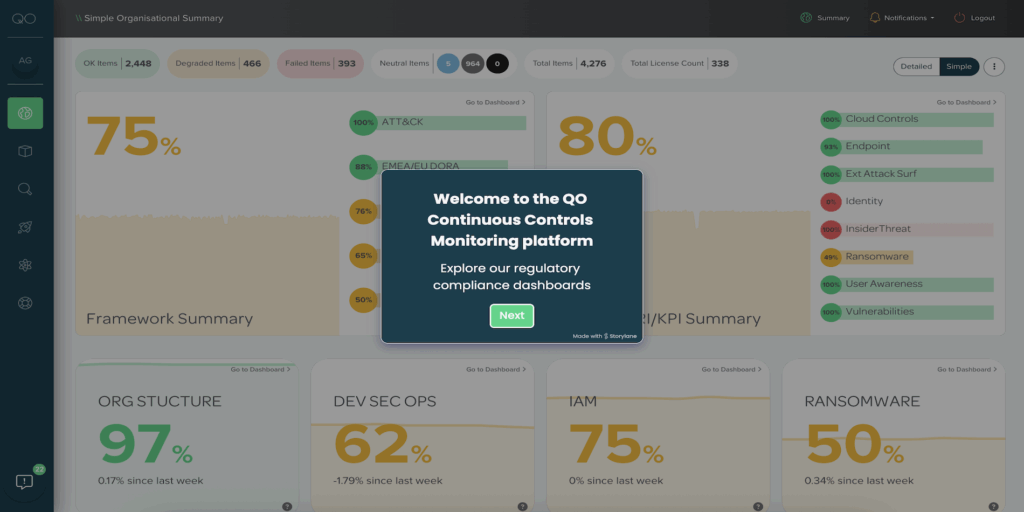
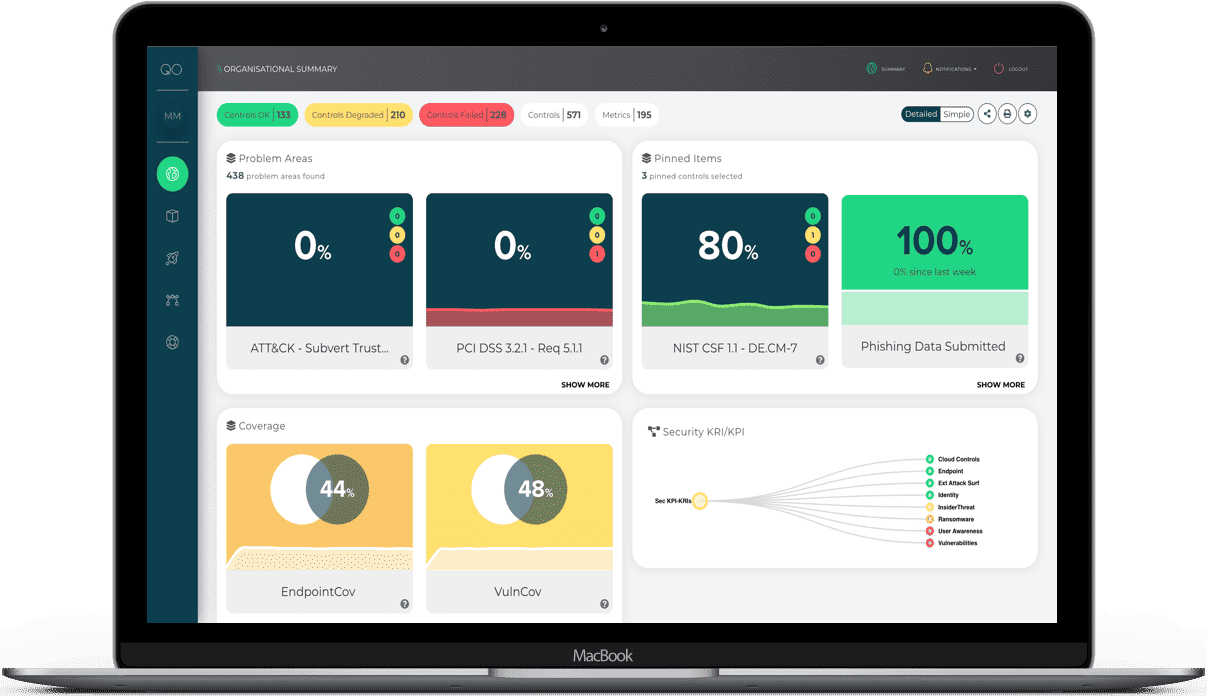
Navigate our guided tour to experience first-hand how our CCM platform provides complete oversight into your cyber security, risk and compliance posture. We can connect to any data, monitor any control and align to any framework.
You can expect to see;
- How to navigate the platform
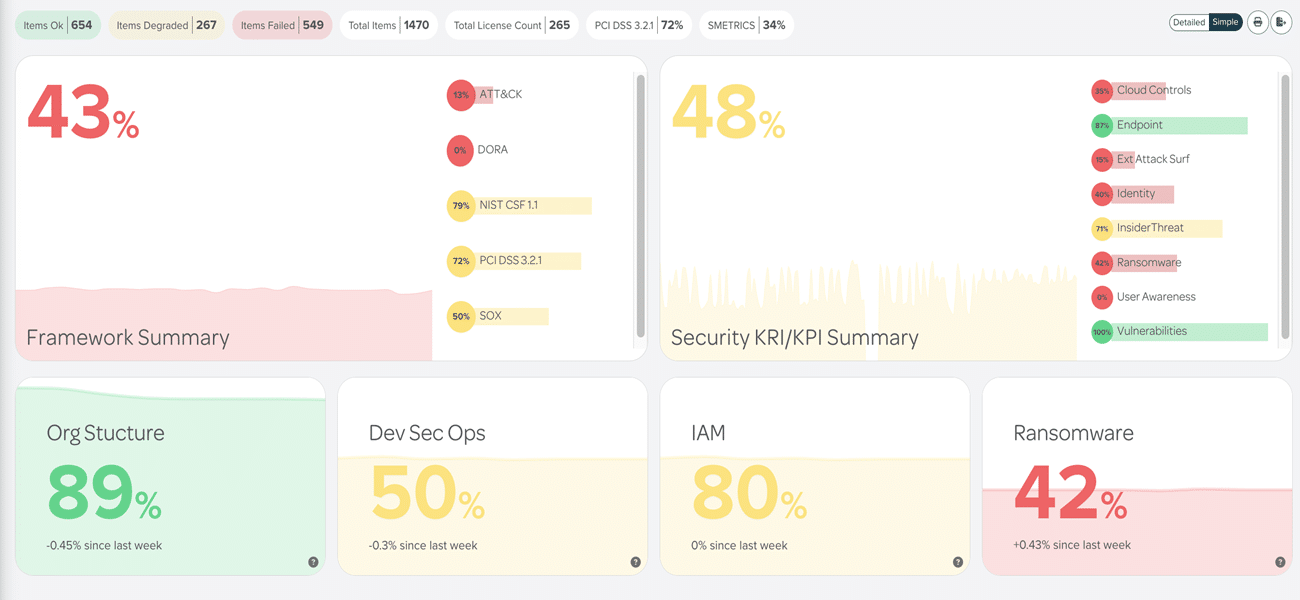
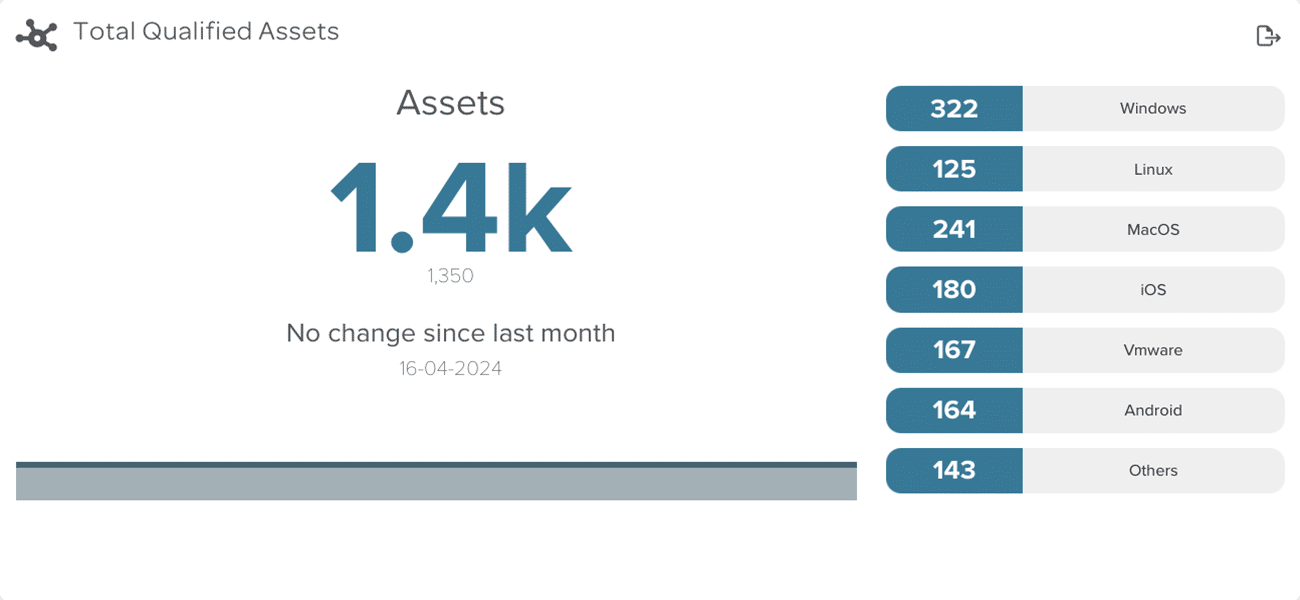
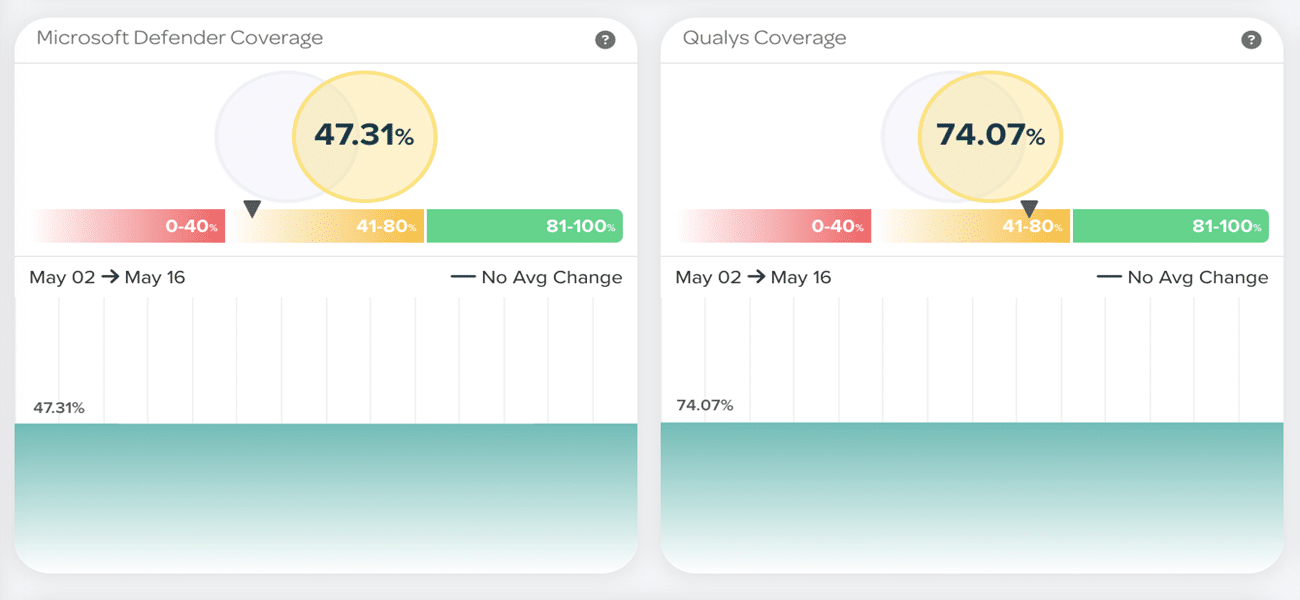
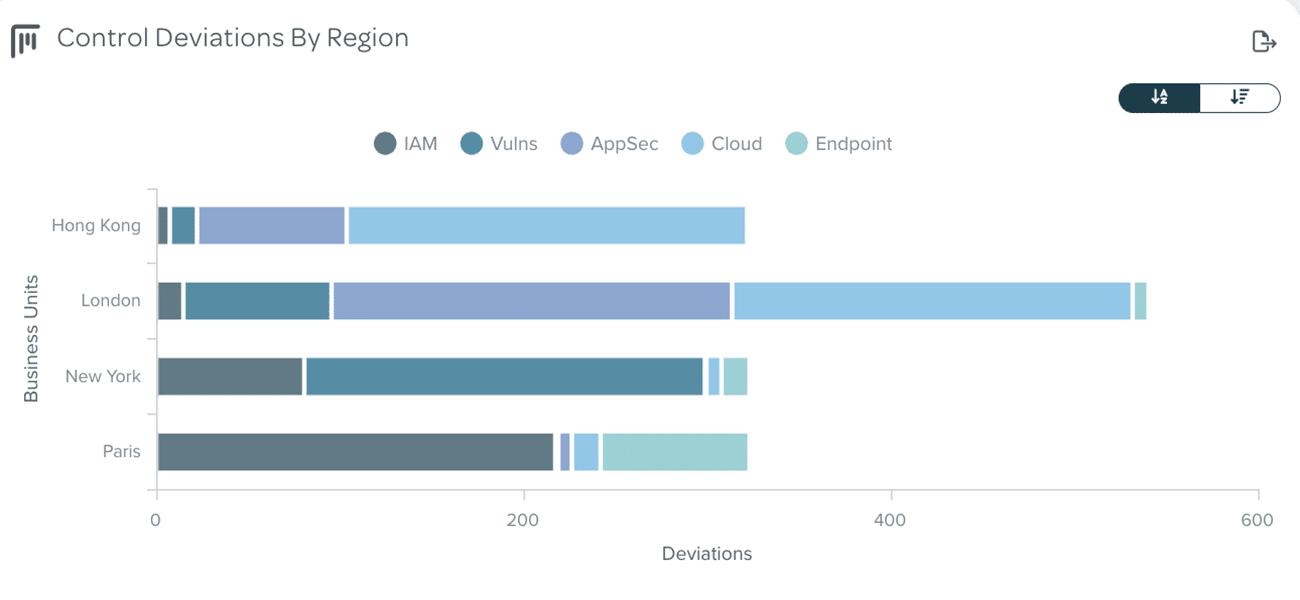
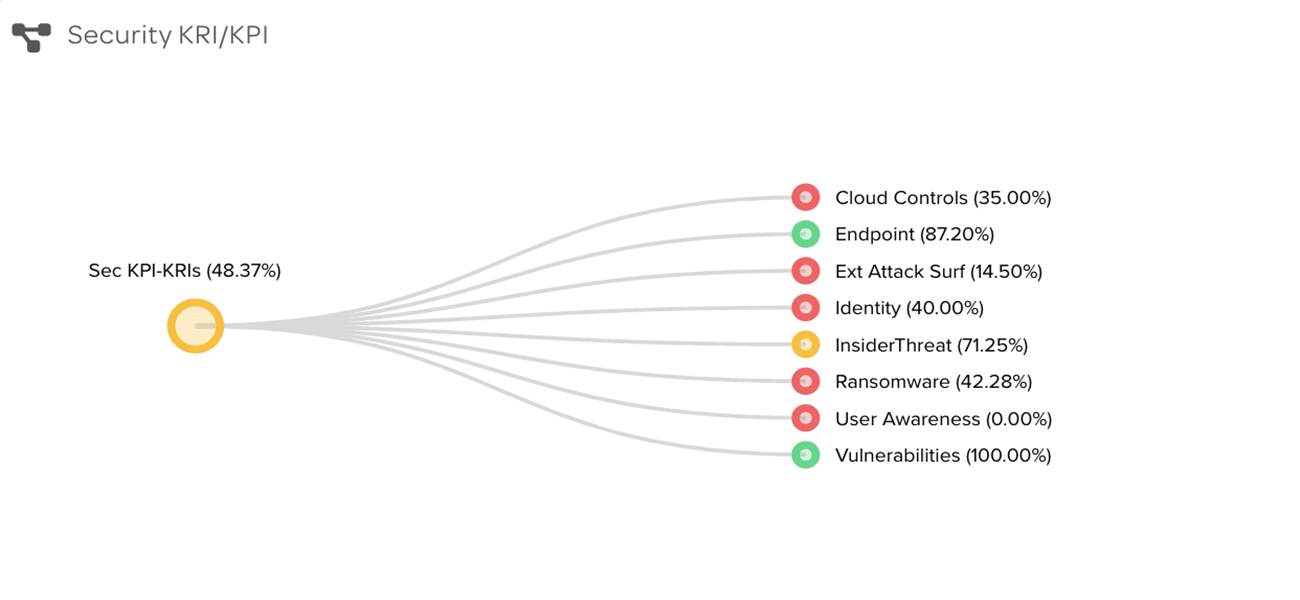
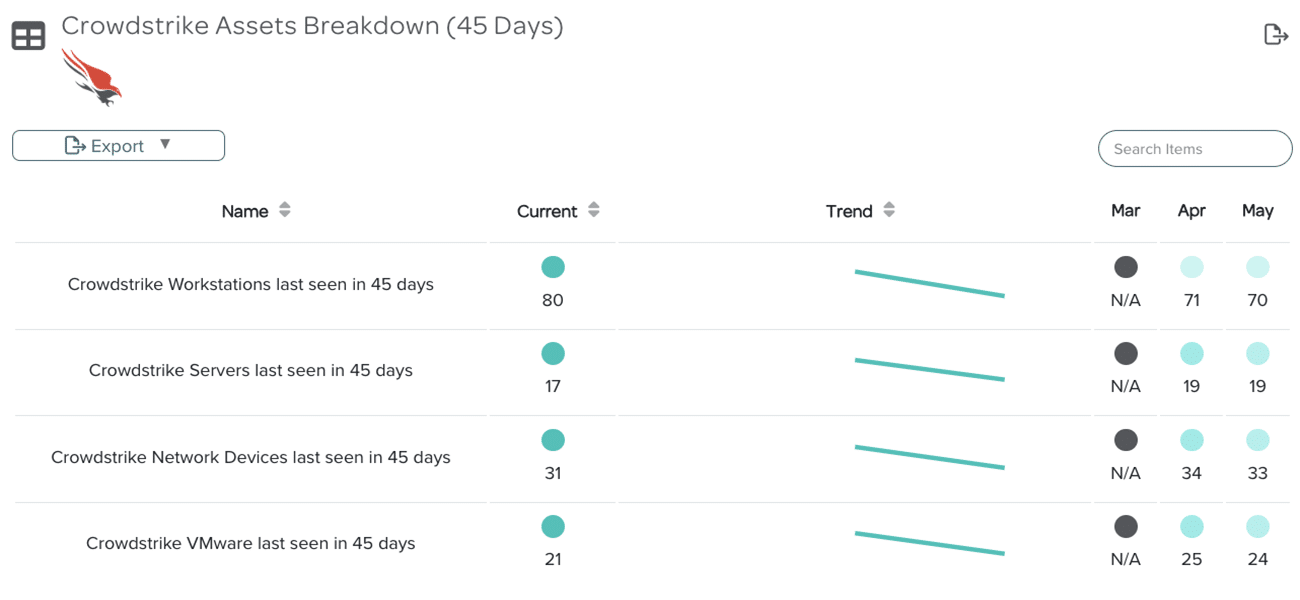
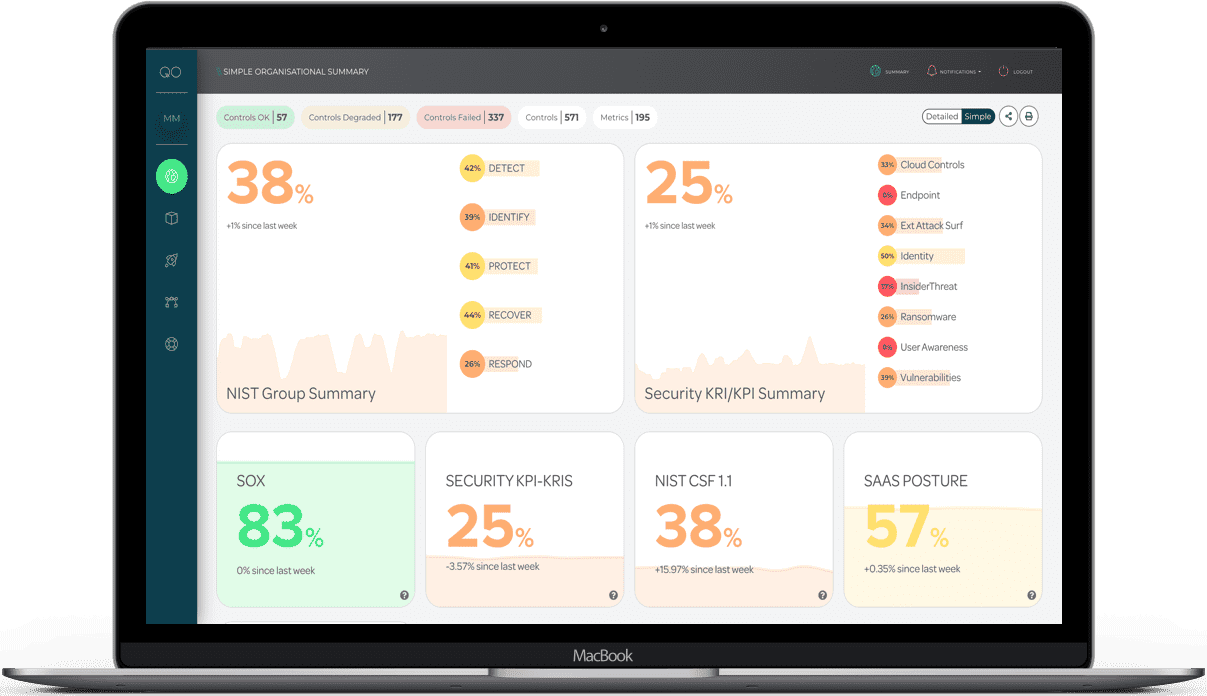
- Overview of summary & detailed dashboards
- Ransomware & compliance dashboards
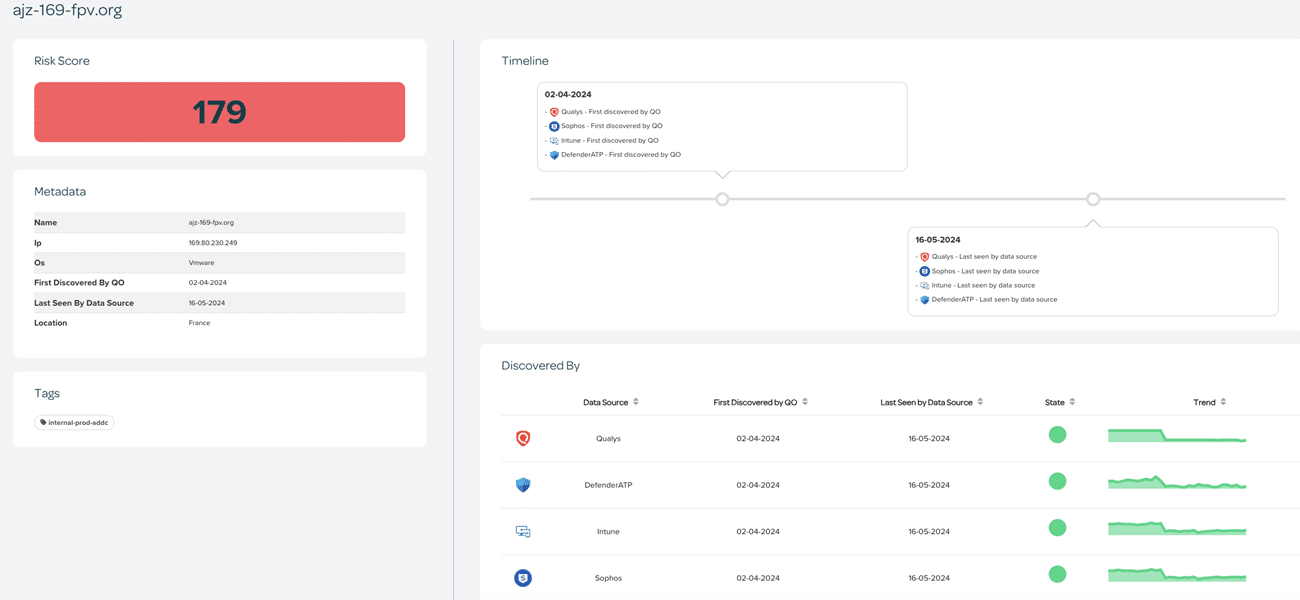
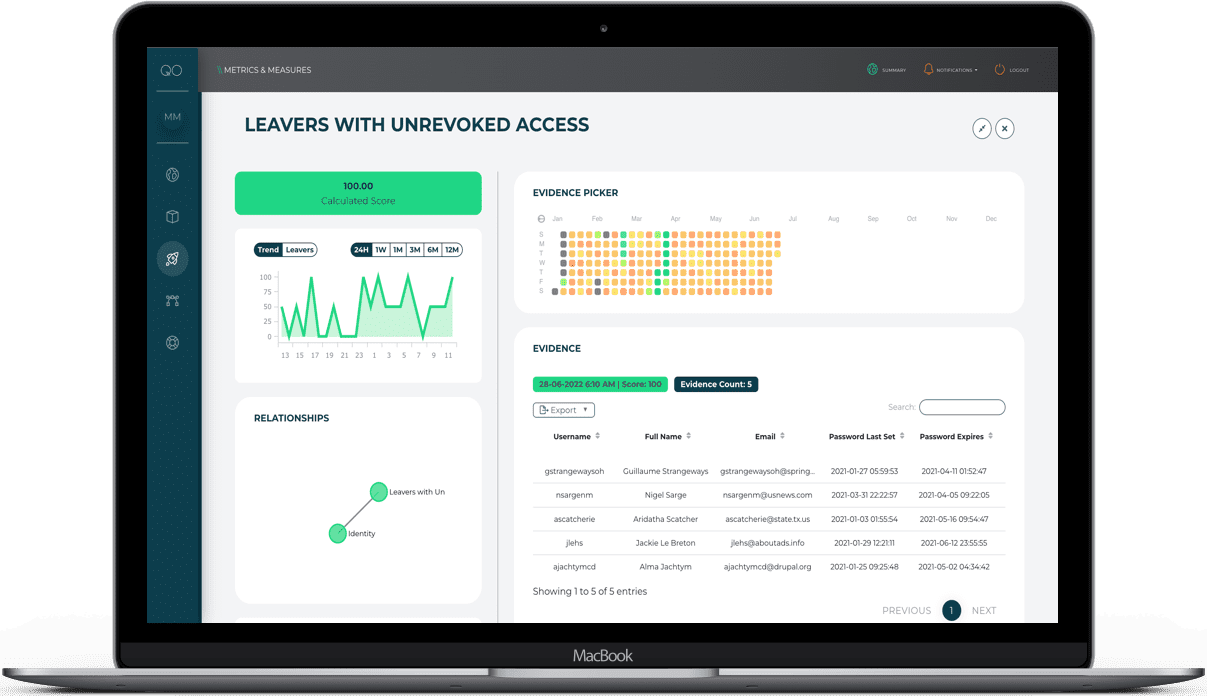
- How to drill into the evidence of the reports
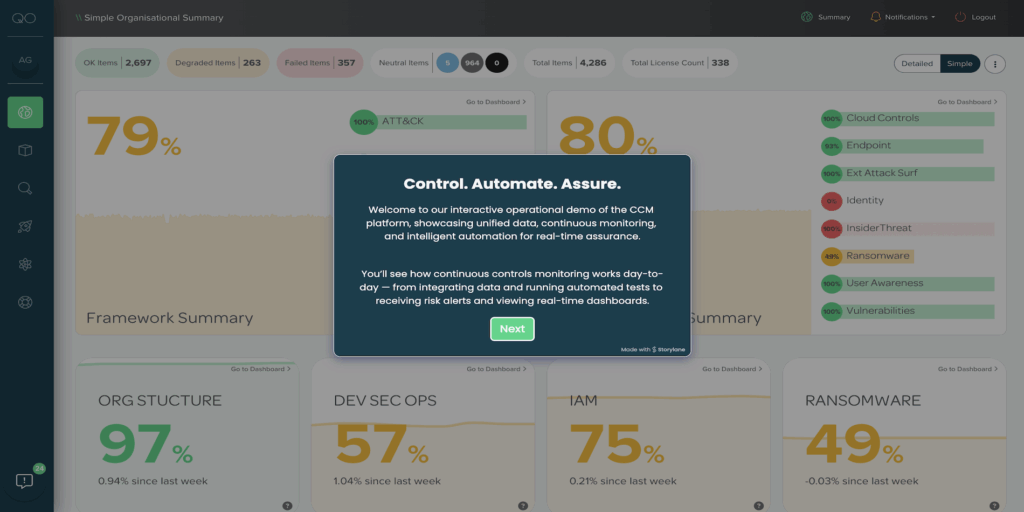
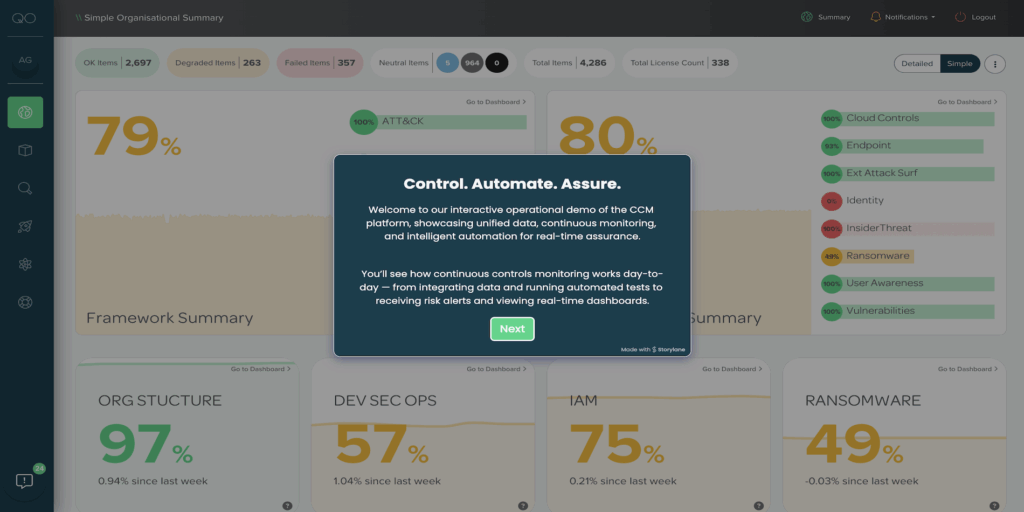
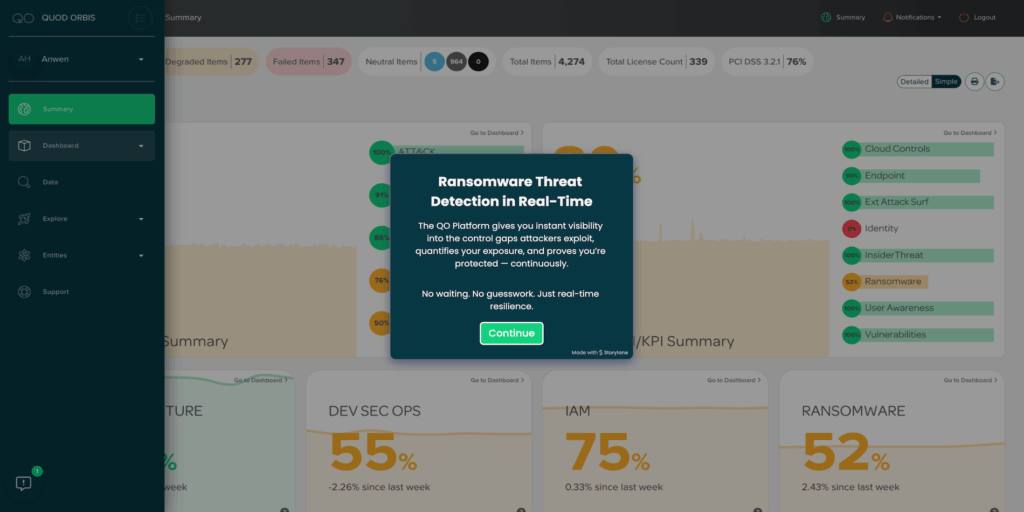
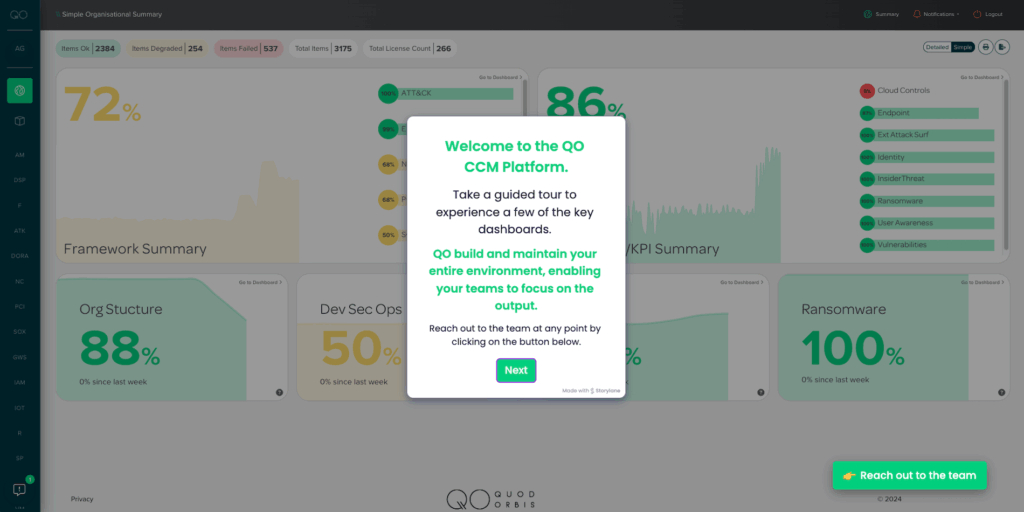
Our Continuous Controls Monitoring (CCM) platform allows you to see and understand your security and risk posture in real time. You get complete controls visibility with automated, continuous monitoring of all your security controls, continuous compliance, whilst benefitting from our unique service wrap.


Get more, see more, achieve more
-
What you get
Real-time security assurance and peace of mind
Get security assurance and peace of mind through accurate real-time data from all your controls, with early awareness of potential problems – all via a managed CCM platform that includes ongoing service from Quod Orbis experts.
-
What you see
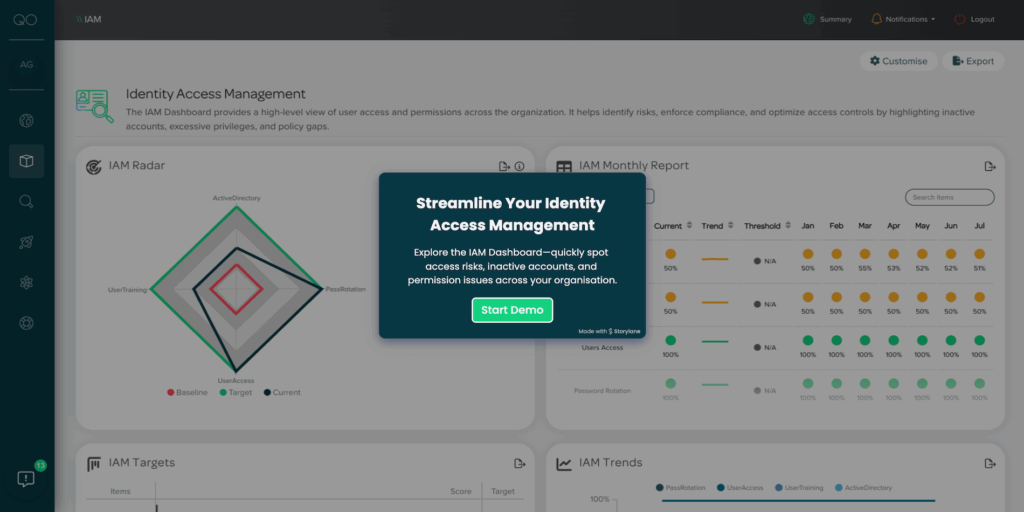
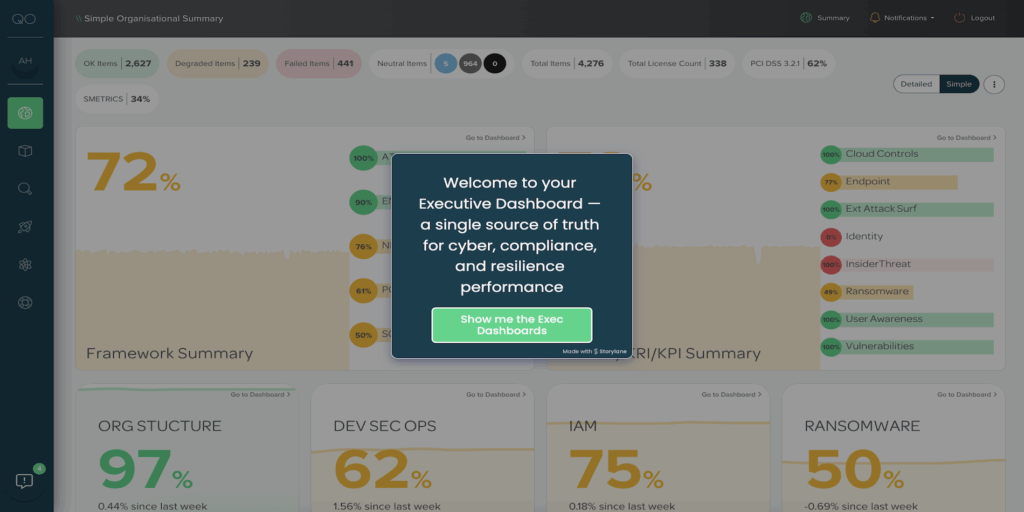
The complete security and risk picture, all in a single source of truth
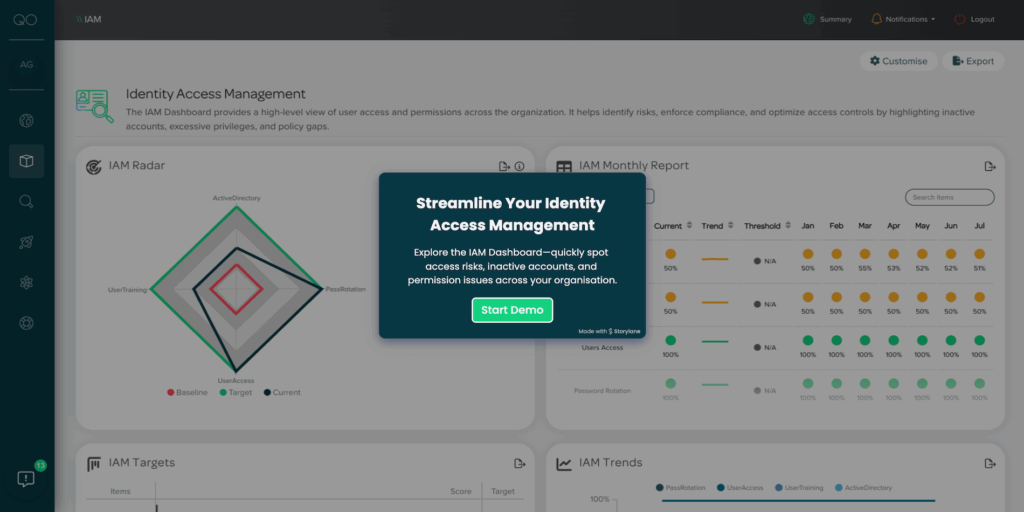
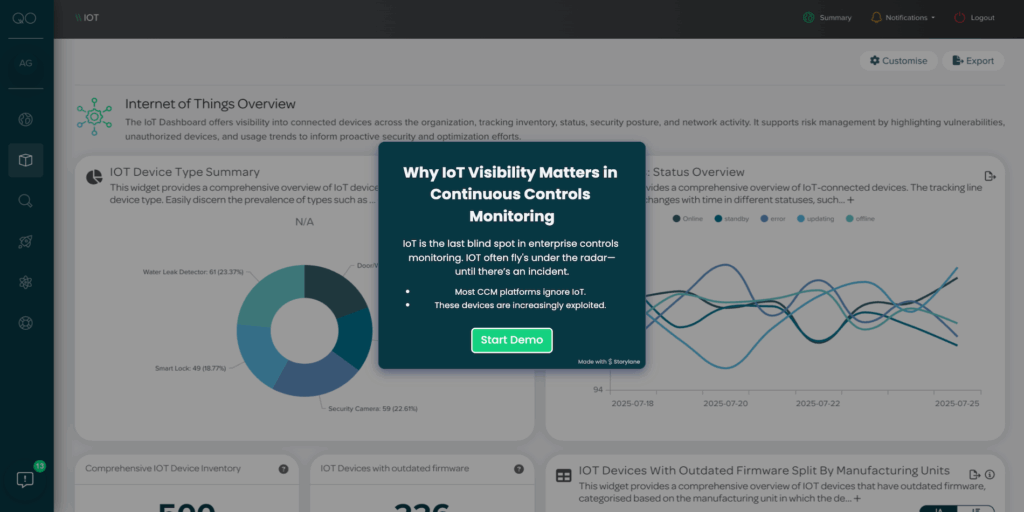
See customised and personalised visual controls status 24/7 from across your organisation via a configurable, user-friendly dashboard that’s as relevant for CxOs as it is for IT, security, risk, audit and compliance roles.
-
What you achieve
Continuous compliance, increased cyber resilience, reduced risk and cost
Achieve automated assurance and continuous compliance status in real time – all with significantly reduced risk and cost for protection of your business operations, revenue, reputation and profits.
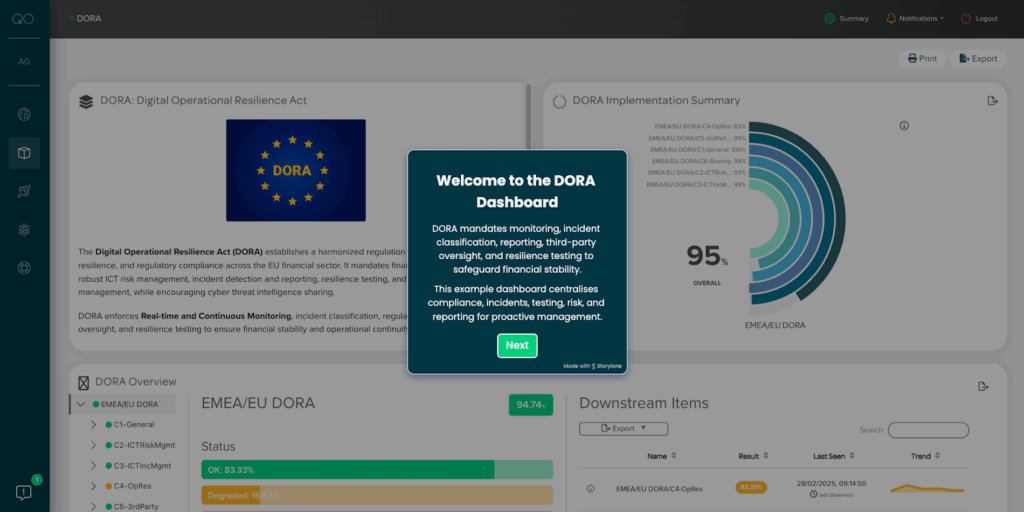
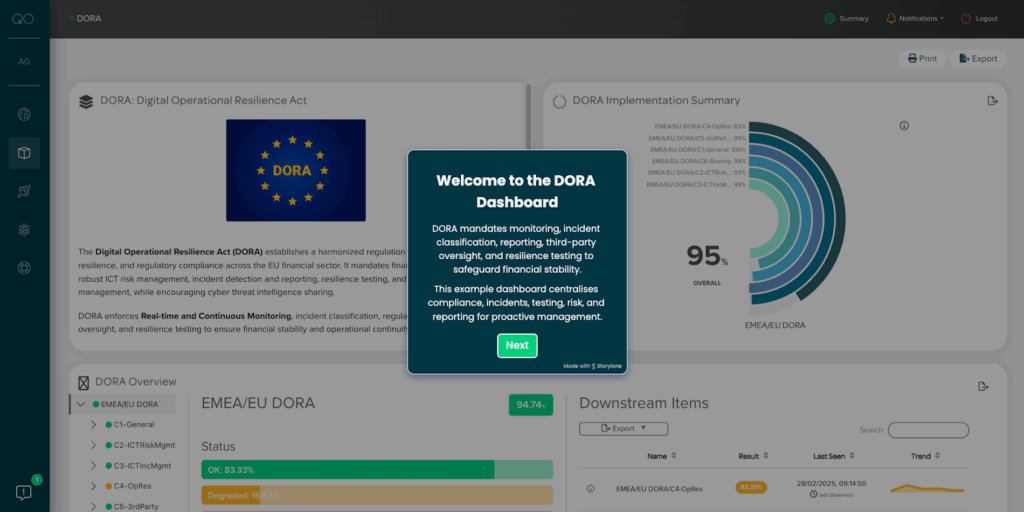
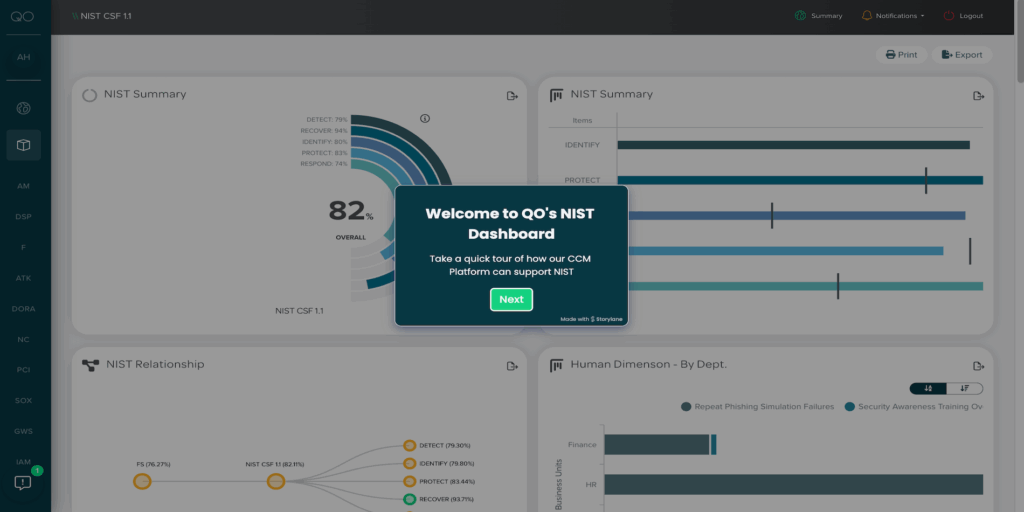
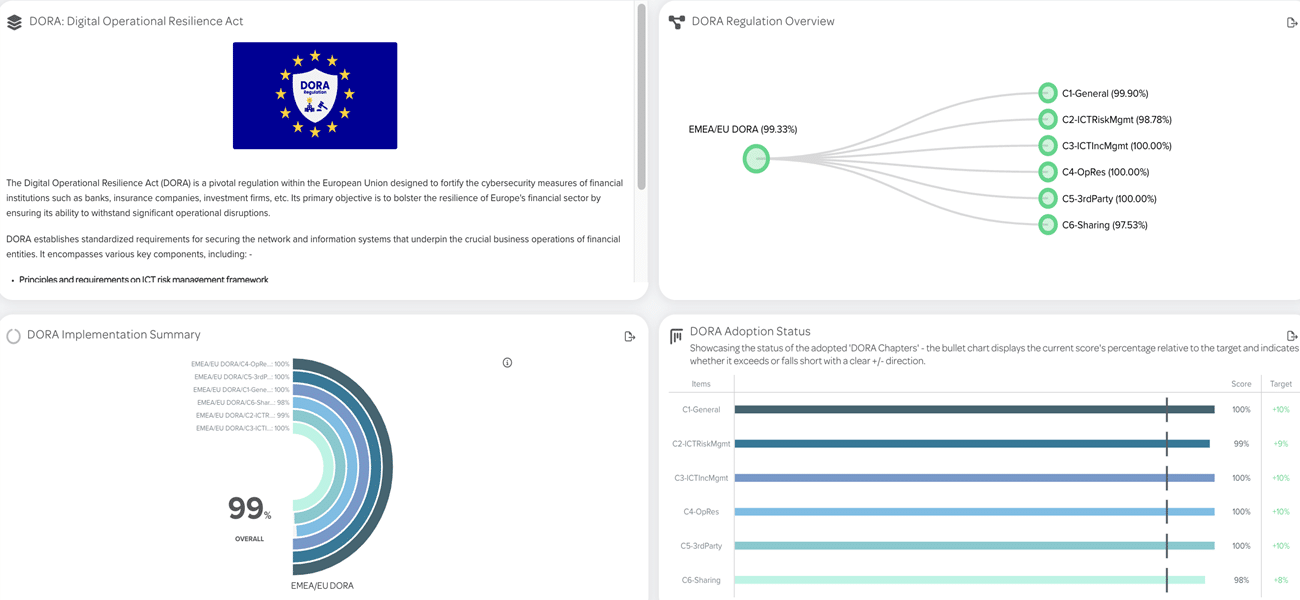
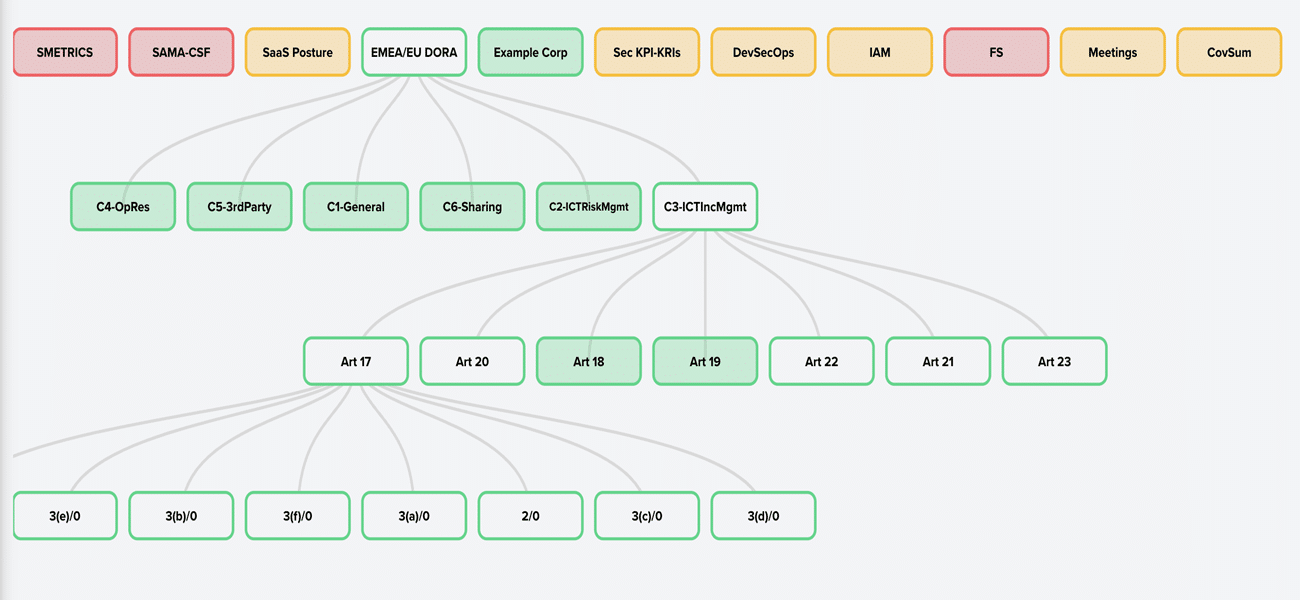
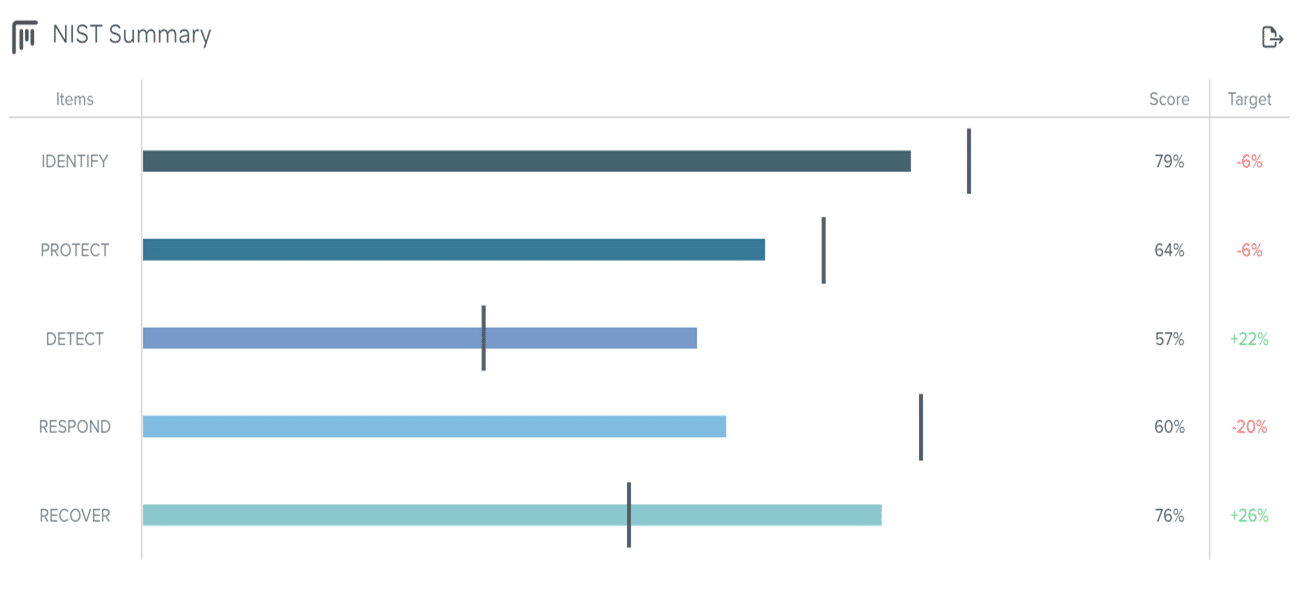
Any framework, any control
Compliance with all major frameworks, standards and regulations
Quod Orbis CCM enables faster, easier organisational awareness and compliance with all major international security frameworks, standards and regulations. These include:










The QO service wrap
Our Service Wrap provides your business with the agility and flexibility to continuously evolve with you as you need it, by maintaining accuracy in the platform so you have 100% confidence in the information you view.
Benefits of our Service Wrap with our CCM Platform include;
- Access to controls experts
- Your own Customer Success Manager
- Ongoing updates
- QO experts monitoring your platform
The QO service wrap
Our Service Wrap provides your business with the agility and flexibility to continuously evolve with you as you need it, by maintaining accuracy in the platform so you have 100% confidence in the information you view.
Benefits of our Service Wrap with our CCM Platform include;
- Access to controls experts
- Your own Customer Success Manager
- Ongoing updates
- QO experts monitoring your platform
Featured Use Cases
Whether you’re a decision maker in Security, Risk, Compliance, Audit, or operate within the IT Team, our CCM will help you drive rapid improvements and ROI.
Explore our Use Cases to discover the ways in which Quod Orbis CCM can transform how you deliver on your remit.
ASSURANCE
For teams in Cyber Assurance, Cyber Oversight, Governance and board reporting, our CCM platform provides the confidence that data is current, accurate and controls are working effectively.
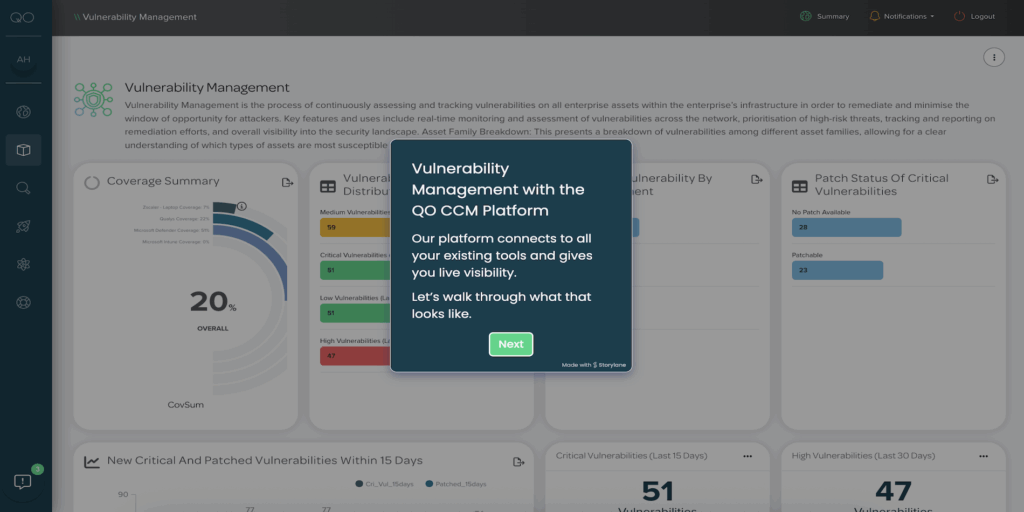
VISIBILITY
From operational to board level, our Continuous Control Monitoring platform provides complete, continuous and consistent visibility of your controls and metrics via role-specific dashboards.
RISK
The Quod Orbis CCM reduces risk by moving from a manual, point-in-time (typically annual) view to an automated, real-time view for governance, risk and compliance, enabling cyber risk quantification.
COMPLIANCE
With Quod Orbis CCM, your GRC/IRM programmes really come to life, as automated, continuous compliance replaces manual attestations for huge time and cost savings .
AUTOMATION
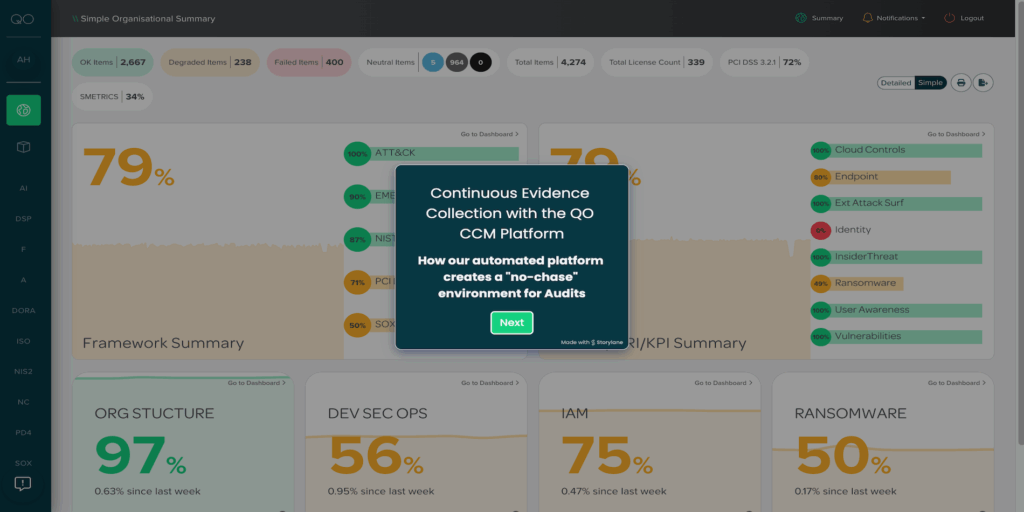
Without CCM, controls management and cyber security, risk, audit and compliance activities are typically point-in-time, manually intensive and prone to human error.
MATURITY
Our CCM provides tracking for continuous improvement and increasing maturity. It’s a visible, accurate gauge of your organisation’s operational resilience with actionable intelligence.
Spend your time gaining maximum value from your data, not managing the platform
For any organisation requiring best-in-class security control systems, our CCM managed platform delivers complete visibility of your controls 24/7, security compliance tracking and monitoring, cyber risk management and ongoing support from our cyber security experts.
All of which will save you significant time and budget, dramatically enhance your risk posture, banish audit failure and ‘alert fatigue’.
Cut costs by 75% a year
The Quod Orbis CCM solution can cut audits and compliance costs by around 75% a year*. It also offers remarkably rapid ROI while adding considerable strategic advantage.
Audit automation, increased cyber resilience, continuous compliance
Quod Orbis CCM is a world-leading automated control system that delivers continuous compliance and assurance. This means huge savings for your business in time, effort and cost, and significantly increased cyber resilience and peace of mind.
The Quod blog
Latest cyber security and risk insights, analysis and thought leadership delivered to your inbox
Fancy a chat about CCM?
Book a time that suits you to see our Continuous Controls Monitoring platform.